Tag: Networking
Microsoft releases Source Code for an Open-Sourced OS
Microsoft releases an open source OS which can be downloaded from Microsoft's Azure GitHub repository.
Microsoft has released the source code for an open-sourced operating...
Linux Kernel 4.2 RC8 Now Available For Download!
Keeping up to his regular schedule of Sunday releases, Linus Torvalds, the father of Linux, announced the availability of the eight and last Release...
Testing Video Transmission in Ns-2 Using the EvalVid Framework
Ns-2 is a discrete event simulator targeted at networking research. It provides support for simulation of TCP, routing and multicast protocols over wired and...
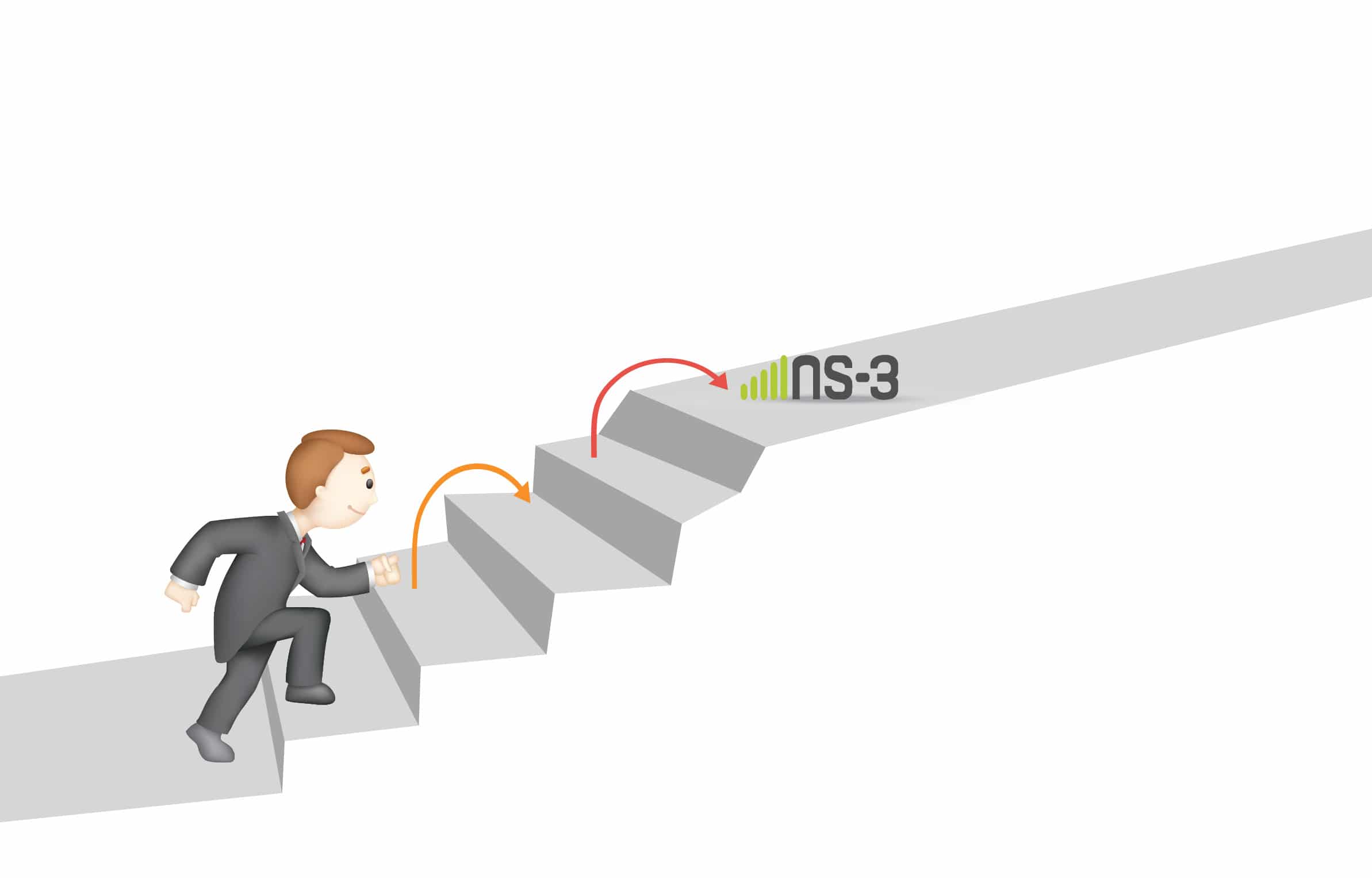
Taking the First Baby Steps in Ns-3
Ns-3 is a network simulator for computer network simulation, used mainly for research and educational purposes. This article is the third in the series...
An Introduction to ns-3
This article is the first in a new series on ns-3, which is a discrete event network simulator for Internet systems, meant primarily for...
The next step to mastering ns-3
In this, the second article on ns-3, the author touches upon Doxygen, Waf, socket programming, etc.
Let us continue our journey to master ns-3. We...
Qt5: Console Applications and Networking
Continuing with the series on Qt5 programming, this article takes the reader on to writing code and building a console application, which is also...
Open Up or Lose Out
"An open network is integral to innovation and efficiency"
It has never been more exciting to be in data centre networking as new technologies such...
Test Your Troubleshooting Skills With Trouble-Maker
Trouble-Maker, as the name suggests, is a Linux tool that, when installed in a system, randomly selects a problem from its list and actually...
Build Your Own Private Cloud with Eucalyptus
Now empower your organisation the open source way! Learn about the Eucalyptus private cloud platform and then go on to install, configure and work...