Cyber security is an incredibly complex, volatile and delicate issue, with systems constantly under attack by an assortment of entities from around the world. Let’s examine some open source software tools, both new and old, which keep our systems safe.
2018 could well be labelled the year of the data breach. This is solely due to the high profile incidents involving broken systems, malpractices and murky underhand dealings pertaining to data security. In 2018, the Goliaths of tech came under intense scrutiny, given the very public revelations of unethical business practices and the purported exploitation of their status at the apex of the tech pyramid to (allegedly) indulge in dubious practices in dealing with sensitive user data. From the US elections to the US government formally accusing North Korean actors of perpetrating the Sony hack, the past year has been a revelation. Data breaches often result in high-tension situations between nations. In fact, as a cyber security consultant stated in a Hacker-noon post, instead of naming 2018 as the ‘Year of the data breach’, we may as well switch to announcing the biggest breaches of the year since they only seem set to increase in severity, year on year.
In such an atmosphere, systems administrators and cyber security engineers have the additional responsibility of not only ensuring the encryption and security of user data but also its ethical use, according to what constitutes ‘fair practices’ for the business in question. To aid these endeavours, here is an attempt to break down the list of cyber security tools that are free, open source and available for use in business-oriented use cases, including some specialised ones for corporate networks.
In a sector that is bustling with activity, we have a surprising new entrant contributing a seemingly well-built open source tool for network security – the National Security Agency (NSA) of the United States of America!
New age tools
Let’s first look at the new entrants in the security domain, along with a detailed breakdown of their features and performance in creating a more secure network for enterprise and personal use cases.
Ghidra: The most recent contender on this list, NSA’s Ghidra, is somewhat a surprise, last-minute entrant, considering it was only released a few days before the writing of this article. Not much is known about it yet, but at first glance, it seems to be a comprehensive reverse engineered framework for software, built to provide deep insight into malicious code as well as a better understanding of vulnerabilities in systems and computer networks.
To quote the GitHub description verbatim, this framework includes a suite of full-featured, high-end, software analysis tools that enable users to analyse compiled code on a variety of platforms including Windows, MacOS and Linux. Its capabilities include disassembly, assembly, decompilation, graphing and scripting, along with hundreds of other features. Ghidra supports a wide variety of process instruction sets and executable formats. It can be run in both user interactive and automated modes.
In addition, there is the functionality to allow users to develop their own Ghidra plugin in Java or Python. NSA says the entire idea behind its release was to foster an ecosystem and community efforts around this toolkit that would allow a better brand of talent to be available from the student and professional communities, leading to an overall benefit to the field. Sceptics claim this is a load of hogwash, but still don’t know enough about Ghidra to counter the NSA’s claims, effectively. The fact remains that the NSA has given us a lot to look into, and more opinions will most definitely emerge as the software tool is dissected and scrutinised further!
Osquery: Released by Facebook, Osquery uses SQL powered operating system instrumentation, monitoring, and analytics. Essentially, it exposes the operating system as a high performance relational database and allows you to write SQL based queries to explore the data within the operating system. In Osquery, the different processes, loaded kernel modules, open network connections, browser plugins and file hashes are treated as elements within an SQL table. It is fairly simple to then understand its schema and query the appropriate element or subset thereof.
Facebook claims there are two main features that users should know about Osquery:
- It runs everywhere and is entirely platform-independent due to there being no dependencies.
- It is fast and tested for memory leaks, thread safety and binary reproducibility on all supported platforms.
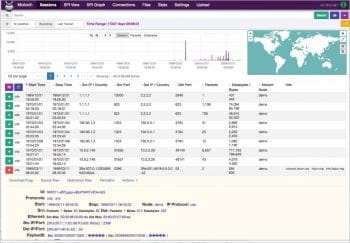
Moloch: AOL’s Moloch is an open source, large scale, full packet-capturing, indexing and database system. The idea, as stated on its website, is that Moloch augments the existing security infrastructure by storing and indexing network traffic in standard PCAP format, while also providing fast indexed access. Moloch is not meant to replace intrusion detection systems (IDS); instead, it provides more visibility. Moloch is built with an intuitive UI/UX which reduces the analysis time for suspected incidents.
The core features work towards reproducibility, an intuitive Web interface, scalability, and the provision of application programmable interfaces to allow JSON and PCAP data to be downloaded directly.
GRR Rapid Response: Google’s GRR Rapid Response expands its remote forensics capabilities in order to be an incident-response framework. Its goal is to support forensics and investigation in a scalable manner, and to allow analysts to rapidly triage attacks and perform analysis remotely, within a short time frame. The software follows a client-server architecture, with the client deployed on systems to be investigated, and the server comprising several components with an API endpoint allowing the scheduling of actions on clients.
The toolkit offers a broad range of functionalities using a collection of libraries including Yara and the Sleuth Kit. It is built to scale and to maintain the granularity of events, even as it offers a high-level overview of an incident. It follows an asynchronous design allowing for automated scheduling, adding to its already-powerful arsenal of functionalities across enterprise use cases.
Security Onion: Kali Linux is a distribution that is typically used for aggressive penetration testing, but when it comes to network security, the Security Onion distro is what many cyber security researchers are using. It has been growing slowly but steadily since its release in 2014 and holds a well-deserved place on this list.
Security Onion comprises a host of tools that come bundled within, saving a significant amount of setup time and effort. The website claims it performs intrusion detection, enterprise security monitoring and log management, and that it includes Elasticsearch, Logstash, Kibana, Snort, Suricata, Bro, Wazuh, Sguil, Squert, CyberChef, NetworkMiner, and many other security tools. The easy-to-use setup wizard allows you to build an army of distributed sensors for your enterprise in minutes.
The old guard
These are the good old tools that have been tried and tested by generations of security researchers and enthusiasts, and still remain popular in the field for a variety of audits and vulnerability scans.
OpenVAS: A comprehensive toolkit spun off from the erstwhile, popular Nessus software (which turned to a proprietary licence), OpenVAS is a tool offering over 50,000 vulnerability scans as documented by Greenbone Networks, since 2007. As per the official website, its capabilities include unauthenticated testing, authenticated testing, various high level and low level Internet and industrial protocols, performance tuning for large scale scans, and a powerful internal programming language to implement any type of vulnerability test.
NMAP: A name that has become synonymous with port scanning, NMAP is a tool that offers a deep set of functionalities targeted at helping users map open ports and running services better, along with the network and operating system fingerprinting at industrial scale. It offers powerful NSE scripts that can detect vulnerabilities and misconfigurations in computer networks.
OSSMAP: The website for OSSEC lists its purpose as watching, alerting and being everywhere. A popular network and host monitoring system, OSSMAP performs log analysis, rootkit detection, real-time alerting, integrity checking, Windows registry monitoring, and active response.
WireShark: WireShark is to network protocol analysis what NMAP is to port scanning. It lets you see what’s happening on your network at a microscopic level and is the go-to solution across many commercial and non-profit enterprises, government agencies and educational institutions.
The Metasploit Framework: Scanning, auditing, and exploits — the Metasploit Framework serves as the primary offensive tool for a number of penetration testers in the field. It does more than simply verify vulnerabilities and manage security assessments, given its wide range of functionalities targeted at security awareness, enabling defenders to stay a step ahead of the game.
The cyber security world is incredibly complex, volatile and delicate, constantly under DDoS attacks by an assortment of entities around the world. However, amidst all these new entrants into the world of NMAP, Kali Linux, OpenVAS and WireShark, we are entering an exciting era in which even more data vigilance is required.












































































