Google has proposed the Supply chain Levels for Software Artifacts (SLSA – pronounced ‘salsa’) to tackle growing supply chain integrity attacks.
While these attacks are not new for the industry, Google says it has developed an end to end framework for ensuring integrity of software deliverable throughout the supply chain, other than the existing point solutions. The SLSA is inspired by the tech giant’s internal Binary Authroization for Borg (BAB), the process Google uses to verify source and implement code ID.
“SLSA’s goal is to improve the state of the industry, especially open source, to protect against the most pressing integrity threats. With SLSA, consumers are informed about the security regime of the software they consume. You can make your choice,” writes Kim Lewandowski, Google Open Source Security Team & Mark Lodato, Binary Authorization for Borg Team.
Automatic creation of auditable metadata
The complicated structure of software development supply chain has made it vulnerable to numerous threats along the source, build and publish workflow. Pointing out to recent sophisticated attacks like CodeCov, SolarWinds, Google says SLSA could have helped.
“We support the automatic creation of auditable metadata that can be fed to the policy engine to give” SLSA certification “to a particular package or build platform,” Google said.
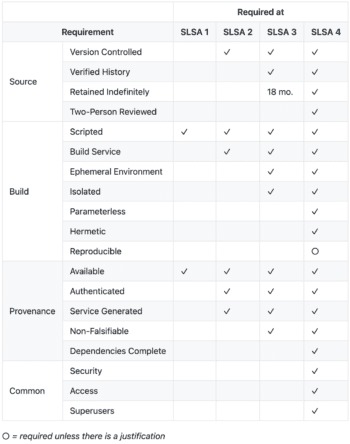
Google defines SLSA as a set of incrementally adoptable security guidelines established by industry consensus and with increase in levels, consumers can trust on highest securities of being untampered and securely trace back to source. SLSA has four levels and software developments are protected as depicted below.