Hyperledger is an open source blockchain platform under the umbrella of the Linux Foundation. It contains multiple frameworks like Indy, Grid, Fabric, Iroha, Sawtooth and Burrow, with support tools like Composer, Aries, Caliper, Quilt, Transact, URSA, Explorer and Cello. Hyperledger’s many frameworks are appropriate for various blockchain architectural purposes unlike other such platforms that do not have variant services.
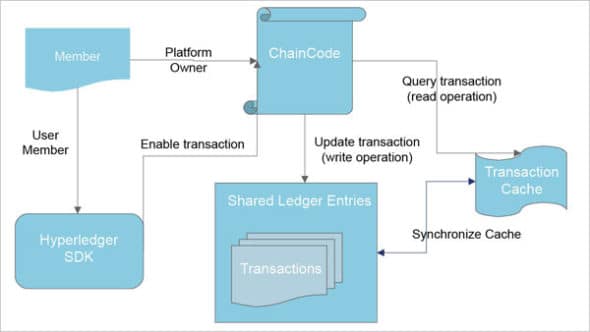
Hyperledger has a unique implementation of functions called Chaincode, which are small pieces of code written in Java, NodeJS or GoLang (like a function in Azure or Lambda in AWS). These can be used to interact with the transactions handled in the smart ledger in a Hyperledger platform. By using this, we can define business logic, such as the execution of rules and the processing logic. Chaincode is therefore a very powerful component of the Hyperledger architecture.
Hyperledger architecture
Hyperledger architecture is unique in blockchain platforms with three-layered components — the infrastructure layer (which contains the ecosystem platform itself), the framework layer that contains the business blockchain frameworks for community development, and the tools layer that contains the accelerators suitable for these framework layers. The services integrated together in the Hyperledger architecture are shown in Figure 1.
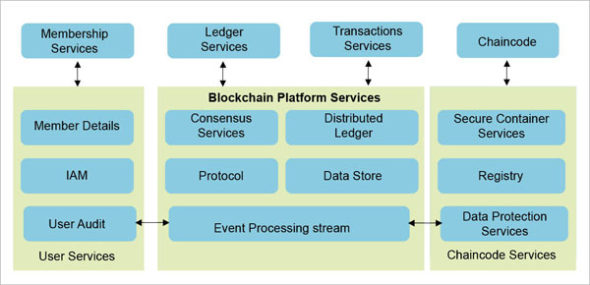
The design philosophy of the Hyperledger frameworks is integrated into the various layers of services as listed below.
Consensus layer: This layer is the brain of the Hyperledger platform, which handles the business logic for transaction management. It ensures the transactions are executed correctly and that the blocks are handled properly.
Smart contract layer: Any request for transaction handling is validated by executing the business logic in the Chaincode function and is taken care of by this layer.
Communications/protocol layer: This layer handles the peer-to-peer message-passing between each of the participating nodes in the platform, in order to manage the transactions in the shared ledger copy in the blocks.
Data layer: All the data handling activities including the enrichment of transactions, audit trails of message processing and transaction states are managed in this layer. It also has crypto abstraction, which enables data to be securely stored by using different crypto algorithms. This layer ensures the identity services layer, establishing the root of trust in the blockchain instance.
Identity services layer: Membership registration services are handled in this layer to ensure authorisation and authentication of member access, across nodes in the platform.
API layer: All service interface capabilities to third party tools and frameworks are enabled by this layer to handle synchronous calls of requests and responses to the blockchain platform.
Policy services layer: This enables the governing principles, and caters to the business policy of the underlying blockchain platform.
The open source Hyperledger software development community
Hyperledger project development and consensus management is governed by the Hyperledger Architecture Working Group. This serves as a cross-project forum to bring together the community members and architects to develop the community and implement the underlying framework. For example, consensus can be implemented with different lottery based algorithms and decided by the use case implementation of the frameworks defined by the working group. Hyperledger Fabric runs a voting based algorithm, Hyperledger Indy runs Redundant Byzantine Fault Tolerance (RBFT), Hyperledger Iroha runs the Sumeragi algorithm (permissioned server reputation system) and Hyperledger Sawtooth runs the Proof of Elapsed Time (PoET) algorithm as defined by the Working Group Community to enable different frameworks that are enabled for different use cases.

Hyperledger smart contracts
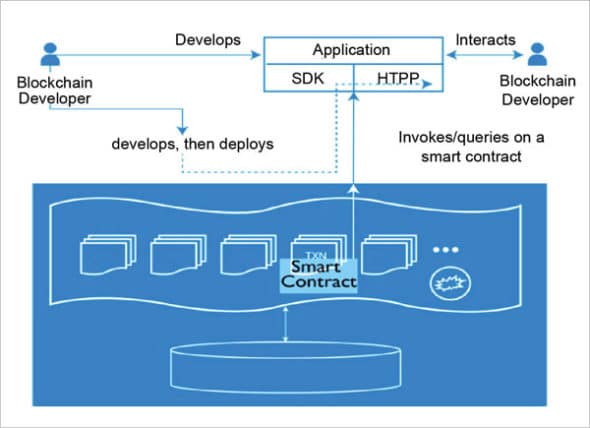
Chaincode is a useful function in the Hyperledger platform, and helps to manage the state of the transaction and its associated business processing functionalities. Therefore, it typically acts as a ‘smart contract’ in the context of the Hyperledger platform, and it can be used to query or update transactions in the platform. With this facility, Hyperledger provides a modular architecture, can be deployed using container architecture and hence offers the advantage of scalable and high-performance architecture.
Chaincode is the central implementation of how the transaction is to be handled and managed by the platform owner. It is a small piece of code written as functions on how to handle the transactions, including the logic to execute, as well as the processing states of the transaction and the application handling capabilities, including the framework to be invoked through the API layer.
Hyperledger Fabric
Hyperledger Fabric is a modular blockchain framework that is the de facto standard for enterprise blockchain platforms delivering a high degree of confidentiality, resilience, scalability and flexibility. It was actually proposed to support varied pluggable implementations of different components and accommodate the complexity that exists across the entire economic ecosystem.
Hyperledger Fabric doesn’t require expensive mining computations to commit transactions; so blockchains can scale up with low latency. Hyperledger Fabric is different from other blockchains like Ethereum or Bitcoin, not only because of its type, but also its internal functional mechanism.
Hyperledger Fabric is based on the following key design features.
- Chaincode: Programs are written in a higher level language that executes against the ledger’s current state database.
- Channels: These are communication subnets for sharing information among members in the network in a highly confidential manner.
- Endorsers: Used for validating the transactions.
- Membership services providers: Provide identity validations and authentication processes by issuing and validating certificates.
Hyperledger Sawtooth
Sawtooth is an open source blockchain platform founded under Hyperledger. It facilitates a modular and flexible platform for implementing transactions based updates to a shared state between untrusted parties coordinated by consensus algorithms. It simplifies blockchain application development by separating the core system from the application domain. It allows flexibility to the applications to choose the transaction rules, permissioning, and consensus algorithms that support unique business needs. Sawtooth is built to solve the challenges of permissioned (private) networks. Clusters of Sawtooth nodes can be easily deployed with separate permissioning. There is no centralised service that could potentially leak transaction patterns or other confidential information.
Hyperledger Sawtooth supports creating and broadcasting events. This allows applications to:
- Subscribe to events that occur related to the blockchain, such as a new block being committed or switching to a new fork.
- Subscribe to application-specific events defined by a transaction family.
- Relay information about the execution of a transaction back to clients without storing that data in state.
Figure 4 highlights the Hyperledger Sawtooth architecture.
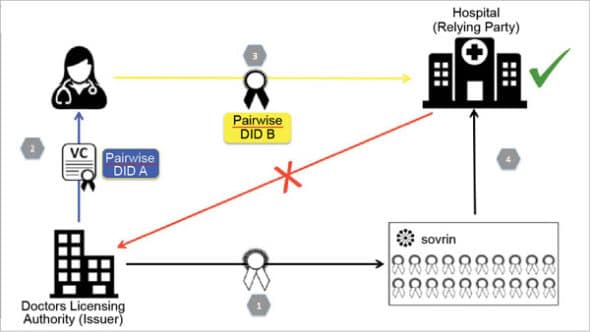
Hyperledger Indy
Hyperledger Indy is another distributed ledger that has been especially designed for decentralised digital identity management. It is termed a public permissioned blockchain network for identity, with privacy features. With Indy, identity owners take full control of their personal data in order to expose only selected information or avoid exposing personal data. It provides advanced security features in terms of privacy, data breaches and identity theft.
It is composed of the following projects.
-
-
- Indy Node: This is an Indy-Plenum based implementation of the distributed ledger with Redundant Byzantine Fault Tolerance (RBFT).
- Indy-sdk: This is a client library to interact with the Indy network.
- Indy-crypto: This is based on the Apache Milagro Cryptographic Library (AMCL) and supports C, RUST and the Python API.
-
Figure 5 highlights the Hyperledger Indy architecture.
Hyperledger tools
Hyperledger Caliper
Hyperledger Caliper is a benchmarking tool for blockchain as it allows users to measure the performance of blockchain implementation with predefined use cases. It provides numerous reports, and contains performance indicators when used with varied blockchain solutions like Hyperledger Besu, Burrow, Ethereum, Hyperledger Fabric, Iroha and Sawtooth.
The benchmarking parameters in Caliper are as follows.
- Success rate: It allows end users to determine how many out of all submitted transactions have been processed successfully and written on the blockchain.
- Throughput: This reports the number of transactions per second processed by the underlying blockchain network.
- Latency: This measures the rate at which the transactions are processed and written on the ledger.
- Resource consumption: This report highlights how many resources are consumed by each Docker container.
Hyperledger Ursa
Ursa is a shared cryptographic library that enables people to avoid duplicating other cryptographic works and enhance overall security. Ursa provides open source blockchain developers with reliable, secure, and pluggable cryptographic implementations.
The major artifacts of Ursa are:
- C-callable library interface
- Rust Crate
Ursa is divided into two sub-libraries: Libursa and Libzmix. - Libursa: This has been designed for cryptographic primitives like digital signatures, encryption and key exchange.
- Libzmix: This is a significant way to create zero-knowledge proofs, proving statements about multiple cryptographic building blocks that contain encryption and the signature.




