In an era where data breach costs continue to hit record highs, shifting to a secretless CI/CD pipeline is the most effective step to safeguard digital infrastructure.
Imagine a scenario where a software developer, working late on a Friday evening, accidentally pushes a configuration file to a public GitHub repository. This file contains a single line of code: a static AWS access key. Within less than a minute, automated malicious bots identify this key. By the next morning, the company is faced with a massive bill for unauthorised cloud resources, and sensitive customer data has likely been stolen. In 2026, this is not just a technical error; it is a significant financial and reputational disaster.
The latest industry data confirms that static credentials are the primary point of failure in modern security. According to the IBM Cost of a Data Breach Report 2025, the average breach cost in India has hit an all-time high of `220 million, a 13% annual increase. Additionally, the 2025 Verizon DBIR notes that stolen credentials account for 22% of global breaches and remain a top threat in the Asia-Pacific region. These attacks are especially critical in India, where an average of 263 days is taken to detect and contain them, allowing attackers to remain hidden for nearly nine months.
The traditional method of ‘secret management’, which involves storing passwords in vaults and rotating them every few months, is no longer sufficient. As long as a static key exists, it can be leaked or stolen. The industry is now shifting towards a Zero Trust approach, where we eliminate static secrets entirely in favour of the Workload Identity Federation (WIF).
Instead of using a permanent ‘username and password’ for our automation tools, we use short-lived, cryptographically signed tokens. This shift from ‘something you know’ (a password) to ‘who you are’ (a verified identity) is the foundation of a modern, secure CI/CD pipeline. Let’s examine how this ‘secretless’ handshake works and how it can be implemented to protect your organisation.
The shift from credentials to identity
To understand why ‘secretless’ is the future, we must distinguish between credential-based and identity-based security. Traditional security relies on ‘something you know’—much like a physical door lock. If you have the key, you get in. The system does not care who you are, only that you possess the key.
In a typical CI/CD pipeline, the ‘key’ to your cloud environment is usually a static API password. This method has three major flaws: ‘implicit trust’, where the system cannot distinguish between a legitimate user and a thief using the same key; ‘permanence’, as keys often last for years, giving hackers an ‘infinite’ window of opportunity; and a heavy ‘management burden’, since rotating thousands of keys manually is prone to human error.
In 2026, the industry has shifted to ‘workload identity’. Instead of asking for a password, the system demands proof of identity. Think of this like airport security: you present a passport (identity) to receive a temporary boarding pass (access) valid only for your specific flight. The system verifies who you are before granting a short-lived permission to proceed.
Identity-based security is safer because it uses short-lived tokens that expire in minutes, making stolen tokens useless almost immediately. These tokens provide contextual proof, confirming exactly which repository and branch are requesting access. Since these tokens are created and destroyed automatically, there is no manual work, eliminating the risk of human error during secret rotation. By shifting to identity, we remove the ‘master key’ entirely, leaving no permanent secrets for attackers to steal.
Understanding the OIDC handshake
While the concept of identity-based security is straightforward, the actual process relies on a precise cryptographic conversation known as the OIDC (OpenID Connect) handshake. This ‘secretless handshake’ between GitHub Actions and your cloud provider follows four distinct steps:
1. The request
When the CI/CD pipeline begins, the GitHub runner requests a unique, short-lived OIDC token from GitHub’s identity provider. This token contains ‘claims’, which are verified statements about the job, such as the repository name and the specific branch being used.
2. The handshake
GitHub sends this cryptographically signed token to your cloud provider (like AWS or Azure). This is not a password; it is a digital proof of identity that says, “I am a legitimate runner from this specific project.”
3. The verification
The cloud provider receives the token and checks GitHub’s public keys to verify the digital signature. It then compares the ‘claims’ against a ‘trust relationship’ that is pre-configured. For example, it checks if it is instructed to trust tokens specifically from the sql-learning repository.
4. The reward
Once the identity is verified, the cloud provider’s Security Token Service (STS) issues a temporary security token. This token has a very short lifespan and expires automatically the moment your job finishes, ensuring that no permanent ‘master key’ is ever left behind.
Technical flow
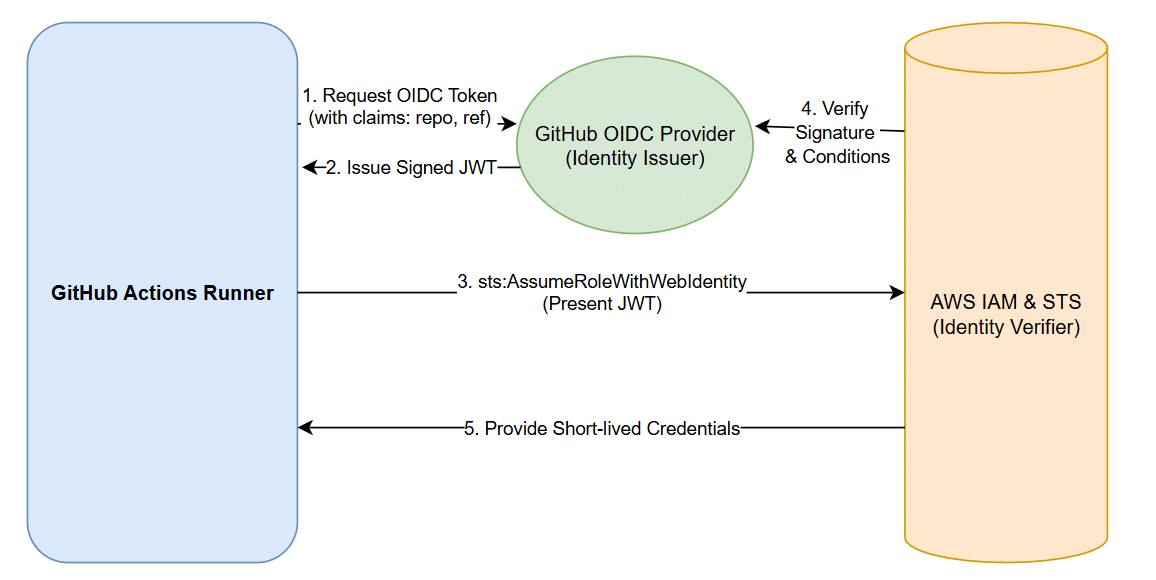
The technical flow of a secretless architecture ensures that sensitive data never sits idle in a configuration file. The process begins inside the GitHub infrastructure, where the runner generates a cryptographically signed JSON Web Token (JWT). This token is unique to that specific job execution.
Once the token is sent to AWS, the IAM Identity Provider performs a real-time verification. It doesn’t just check if the token is valid; it inspects the ‘claims’ to ensure the request is coming from the authorised organisation (name of the GitHub organisation) and the correct repository (sql-learning). If the conditions match, AWS STS generates temporary credentials that expire automatically after the job. This flow, as shown in Figure 1, effectively reduces the ‘blast radius’ of a potential leak to near zero, as there are no long-term keys for an attacker to exploit.
Implementation guide
Implementing secretless architecture involves three primary steps: establishing trust in AWS, defining a secure role, and updating your GitHub workflow. By following these steps, you ensure that no permanent credentials ever leave your cloud environment.
Step 1: Create the OIDC identity provider in AWS
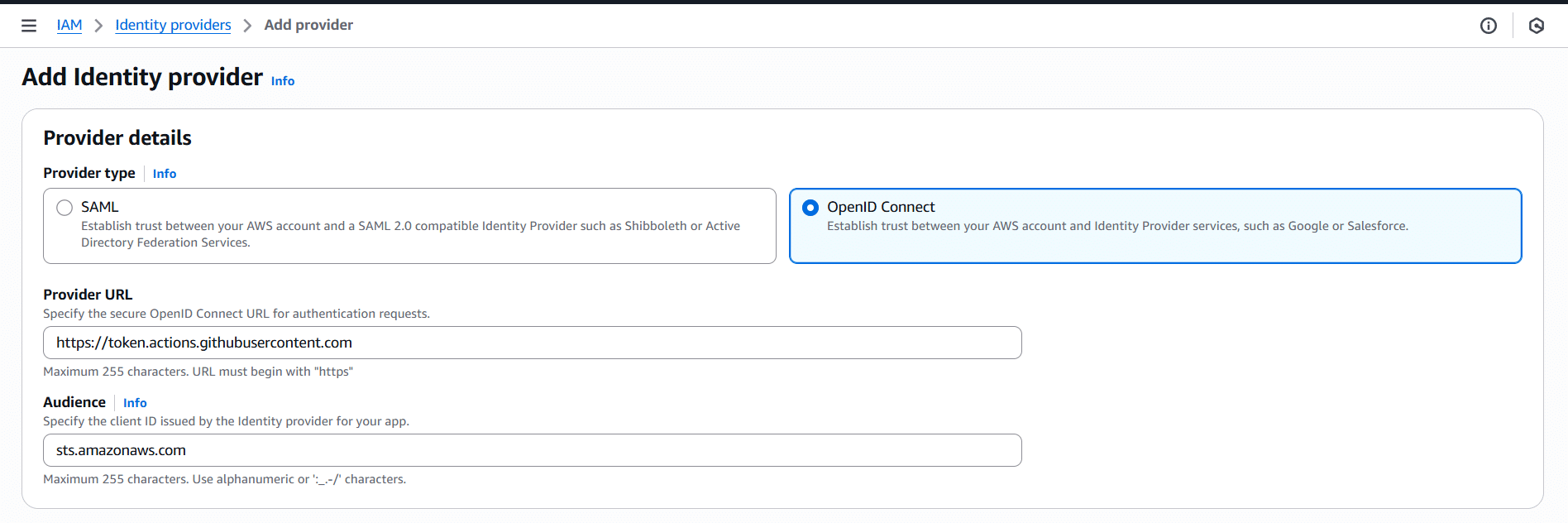
The foundation of a secretless architecture is establishing a ‘trust relationship’ between AWS and GitHub. By creating an OIDC identity provider, you are essentially telling AWS to recognise and trust digital identity tokens signed by GitHub’s official servers. To do this, navigate to the IAM Console, select Identity providers, and click on Add provider. Choose OpenID Connect as the provider type and enter https://token.actions.githubusercontent.com as the provider URL. For the audience, use sts.amazonaws.com. This ensures your AWS environment can securely communicate with GitHub’s identity service as shown in Figure 2.
Step 2: Create the secretless IAM role
Once the trust is established, you need to create an IAM role that the GitHub runner will ‘assume’ to perform tasks. The security of this setup relies entirely on the trust policy attached to this role. Unlike traditional roles, this policy uses a StringLike condition to enforce strict Zero Trust boundaries. It ensures that AWS only grants access if the token’s ‘sub’ (subject) claim matches your specific GitHub organisation and repository. By using a condition like repo:arundotcom/sql-learning:*, you ensure that even if another user knows your Role ARN, they cannot use it from their own GitHub account, as their identity token will not match your specific repository claim. Given below is the code snippet that could be used to create the IAM role:
{
“Version”: “2012-10-17”,
“Statement”: [
{
“Effect”: “Allow”,
“Principal”: {
“Federated”: “arn:aws:iam::AWS-ACCOUNT-ID:oidc-provider/token.actions.githubusercontent.com”
},
“Action”: “sts:AssumeRoleWithWebIdentity”,
“Condition”: {
“StringEquals”: {
“token.actions.githubusercontent.com:aud”: “sts.amazonaws.com”,
“token.actions.githubusercontent.com:sub”: “repo:NAME-OF-THE-ORG/NAME-OF-THE-REPO:ref:refs/heads/main”
}
}
}
]
}
Step 3: Update the GitHub workflow
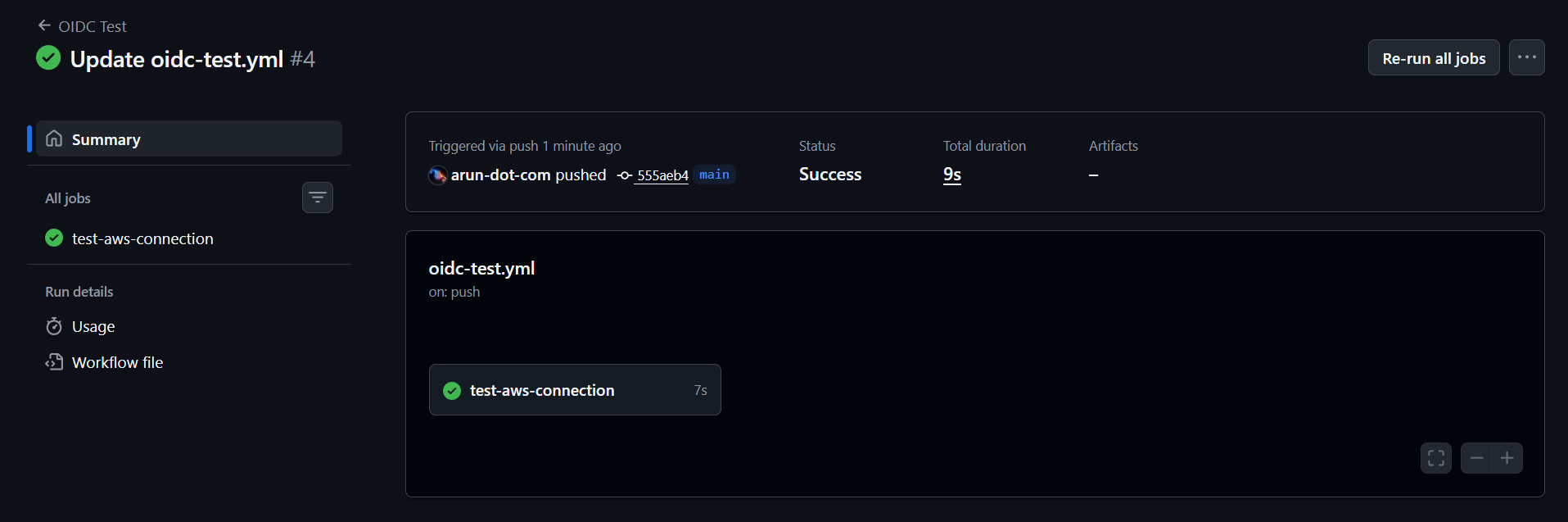
The final step is to configure your GitHub Actions YAML file to request the identity token. You must explicitly set the id-token: write permission in your workflow; without this, GitHub will not generate the OIDC token required for the handshake. In the deployment steps, you use the official aws-actions/configure-aws-credentials action, providing only the Role ARN and the AWS Region. Because the handshake happens automatically in the background, you no longer need to store or reference AWS_ACCESS_KEY_ID or AWS_SECRET_ACCESS_KEY in your repository secrets. When the job runs, the logs will confirm that the runner has assumed the role successfully as shown in Figure 3, proving your pipeline is now completely secretless. The code snippet given below could be used to write the YAML file:
name: OIDC Test on: [push] permissions: id-token: write # This is mandatory for OIDC contents: read jobs: test-aws-connection: runs-on: ubuntu-latest steps: - name: Configure AWS Credentials uses: aws-actions/configure-aws-credentials@v4 with: role-to-assume: arn:aws:iam::549368061164:role/GitHub-OIDC-ZeroTrust-Role aws-region: us-east-1 - name: Verify Identity run: aws sts get-caller-identity
While the manual steps in the AWS Console are excellent for understanding the OIDC handshake, managing these configurations across dozens of repositories is best handled through Terraform. By using the aws_iam_openid_connect_provider and aws_iam_role resources, you can codify your Zero Trust architecture. This ensures that your trust policies remain consistent, version-controlled, and free from the human errors that often occur during manual console configuration. For a production-grade environment, automating this setup is the recommended path to achieve a scalable secretless infrastructure.
Benefits of a secretless architecture
Shifting to OIDC and workload identity is a fundamental improvement that strengthens security while simplifying operational workflows. By moving away from static keys, organisations achieve a ‘win-win’ scenario that follows the ‘principle of least privilege’ and modern Zero Trust standards.
Elimination of credential leaks
Since no static AWS keys are stored in GitHub, there is nothing for a developer to accidentally leak. This effectively closes the #1 attack vector used by botnets to compromise cloud environments.
Automatic secret rotation
OIDC handles credential rotation automatically for every single job. This eliminates the management burden of manually rotating keys every 90 days and prevents production outages caused by expired secrets.
Granular access control
You can restrict access to specific GitHub repositories, branches, or environments. This ensures that even a successful login is limited to a very small ‘blast radius’ for a specific task.
Reduced window of opportunity
Access is granted through tokens that expire in minutes. Unlike permanent keys that can be used for years, these short-lived tokens become useless almost immediately after a job finishes.
Superior auditability
Every action taken in your cloud environment is tied back to a specific GitHub Action run ID in your logs (such as AWS CloudTrail), making it easy to track exactly which code change triggered a specific infrastructure update.
The transition from static credentials to secretless architecture is no longer just a luxury for elite engineering teams; in 2026, it is a fundamental security requirement. By moving away from ‘something you know’ to a verified ‘workload Identity’, we effectively eliminate the risks associated with leaked keys and the operational burden of manual secret rotation. As demonstrated, implementing an OIDC-based handshake creates a robust, automated defence that ensures your cloud environment remains secure, even in the event of an accidental code push.
Adopting this Zero Trust mindset allows organisations to focus on rapid innovation without the constant fear of a catastrophic credential breach. While the initial setup requires a one-time configuration of trust between your identity and cloud providers, the long-term benefits of reduced risk and improved auditability are invaluable.

















































































