When it comes to network security, the first thing that people should be taking care of is their own network. This can be achieved by analysing your data and making sure that no one is intruding on your network. The name PCAP comes from the two words, packet capture. The type of file is the Ethernet packet sniffer, which means that this file format is used by the tools that analyse the network traffic. In this article, I will start with the basics so that even a newbie can easily analyse the data, using the tools mentioned.
The basics
Anyone who is new to network security needs to have a good grasp of the various types of networks. The basic types are TCP (Transmission Control Protocol) and IP (Internet Protocol). We do have many versions of IP and the address varies with the type. This understanding is necessary because, with the help of the IP address, we can determine the location of someone who is mounting an attack. I would suggest you visit some of the links below, which will be helpful to get an understanding of the basics of networking.
http://en.wikipedia.org/wiki/Network_security
http://cse.hcmut.edu.vn/~minhnguyen/NET/Computer%20Networks%20-%20A%20Tanenbaum%20-%205th%20edition.pdf
http://www.cert.org/historical/tech_tips/home_networks.cfm
The best way to get a strong foundation on the subject would be to Google for information, instead of just reading many books. It is better to concentrate on a single book and try out various tools to get a good command over them.
Tools
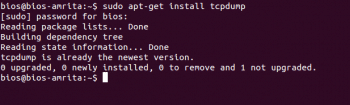
Many tools are available for the analysis of packets, the most basic and most powerful one being tcpdump. It can be installed or updated by using the following command:
sudo apt-get install tcpdump
Many open source tools are available to us but none match tcpdump. It is the best tool to capture and filter packets using a basic C code something that I will discuss briefly, subsequently.
For Windows, there are many tools such as Wireshark and WinPcap. The links are given below.
http://www.winpcap.org/install/default.htm
http://wiki.wireshark.org/Tools
You can get a list of all the tools in open source from here.
http://www2.opensourceforensics.org/tools/network
Everything can be done in the terminal with the help of tcpdump. The remaining tools give us easy access, some benefits and some ready-made features.
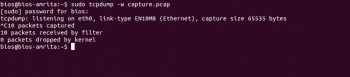
Capturing ones own data
Its very easy to capture your data in Linux by using the terminal (Ctrl+Alt+T) and typing the following command:
sudo tcpdump -w capture.pcap
This command invokes the tool tcpdump and writes the data into the file name capture.pcap (remember .pcap is the extension for the packets captured). This goes on until you give it a keyboard interrupt (Ctrl+C) or temporarily stop the job with Ctrl+Z. Packet capture can be resumed by giving the command fg which is the same as the normal command.
Packet capture can also be done by using online tools such as Wireshark.
Have a look at the man page of tcpdump before going ahead with the article.
man tcpdump
Analysis
I assume that you have a good knowledge of commands (such as | and *) used in the terminal, for this section. If not, here are some links to tutorials that will teach you the basics.
http://linuxcommand.org/lc3_learning_the_shell.php
http://ss64.com/bash/
http://www.pas.rochester.edu/~pavone/particle-www/telescopes/ComputerCommands.htm
The best way to learn about them is to refer the man page when you have a doubt about a particular command.
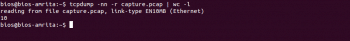
Count of packets
To determine the count of packets in the file, we use the following command:
tcpdump -nn -r capture.pcap | wc -l
Since the file usually contains a large amount of data, instead of using the cat command, it is better to pipe the file to head so that we can get a clear view of it. This can be achieved by using the following command:
tcpdump -nn -r capture.pcap | head
The fields of the PCAP file would be in the following order:
1. Time
2. Network protocol
3. Source IP
4. Source Port
5. Destination IP
6. Destination Port
To concentrate on one of the above fields, remove some of them by using commands for piping and filtering. For example, the following command is used to get only the source IP address and its Port:
tcpdump -nn -r capture.pcap | cut -f 3 -d | head
To filter the file to get TCP/IP and exclude the Layer 2 traffic, add the option tcp or udp at the end of the command:
tcpdump -nn -r capture.pcap tcp or udp | cut -f 3 -d | head
To get only the IP address without the Port, just cut the other columns starting from .
tcpdump -nn -r capture.pcap tcp or udp | cut -f 3 -d | cut -f 1-4 -d . | head
The uniq command
The uniq command can be used to remove repeated lines in the PCAP file, because we are not interested in the same source and destination twice. This command saves you a lot of time and avoids repetition:
tcpdump -nn -r capture.pcap tcp or udp | cut -f 5 -d | cut - f 1-4 -d . | sort | uniq | head
The code below gives the top 10 destination IP addresses. -nr gives the IP address in descending order:
tcpdump -nn -r capture.pcap tcp or udp | cut -f 5 -d | cut - f 1-4 -d . | sort -c | uniq -nr | head
You can try every option available and get your work done easily.
Web tools
If you have a PCAP file you want to analyse but dont have the tools or the sudo password to do so, try online tools such as Wireshark. I am using the small example file which was used for the challenge in picoCTF, where we need to find the destination of the ship from the conversation between the robot and the spaceship. This is a very easy challenge and can be addressed by having a clear look at the conversation (https://www.cloudshark.org/captures/bc1c0a7fae2c).
The alternatives for the cloud shark are given in the following urls.
http://www.wireshark.org/
http://canyouseeme.org/
http://www.lovemytool.com/
http://www.yougetsignal.com/
http://sectools.org/
You can try any of the tools from the above links. Some of them provide tools from the browser itself.