Traditional and off-the-shelf security tools for the cloud may lull organisations into a false sense of being safe from cyber threats. This first article in the two-part series explains why organisations must develop an ‘enterprise cloud security governance strategy’.
“There are two types of companies: those that have been hacked, and those who don’t know they have been hacked.” —John Chambers, ex-CEO of Cisco.
This famous quote highlights the significant threat of cyber attacks in today’s digital landscape. Despite the cloud’s advantages in terms of flexibility and scalability, it introduces new challenges in managing cyber risks. Extending traditional security approaches to the cloud or relying solely on tools or cloud-native security services may not adequately tackle the dynamic nature of modern threats.
Misconfigurations and vulnerabilities in cloud environments are more critical, as they directly expose attack vectors over the internet, which can lead to potential security breaches. Addressing these vulnerabilities requires a proactive approach and a comprehensive strategy that encompasses compliance requirements, risk mitigation, threat detection, and incident response customised to the unique needs of each organisation.
Each enterprise has distinct security needs influenced by factors such as business type, demographics, regulatory obligations, threat landscape, et al. A traditional one-size-fits-all security approach may not adequately address specific requirements. While cloud platforms offer native security services and best practices, depending solely on them without a customised strategy tailored to the organisation’s unique characteristics may lead to a fragmented security posture across the enterprise.
Let’s delve into the intricacies of cybersecurity in the cloud era and explore why traditional cloud security approaches may not adequately address the evolving threat landscape. Why do organisations face difficulties mitigating cloud threats despite adhering to security best practices? What potential gaps exist by sticking to traditional cloud security practices? We’ll also introduce the concept of ‘enterprise cloud security governance strategy’ and how it can potentially address the challenges.
The popularity of cloud and its security implications
Over the past decade, enterprises have rushed to embrace cloud technology, enticed by its unmatched flexibility and scalability. Initially, most organisations prioritised their core business objectives, often neglecting security. However, as they established sustainable operations in the cloud, they confronted increasingly sophisticated cyber threats.
A significant factor contributing to this challenge is the frequent oversight or undervaluation of security during the transitional phase. Some organisations hesitated to allocate additional resources, efforts, and overheads to implement comprehensive security measures, fearing uncertain returns on investment. Consequently, they opted for a minimalist approach, hoping to navigate the complexities with minimal investment.
On the flip side, many enterprises diligently adhere to best practices, promptly addressing security issues identified by their tools and services. This proactive approach often leads them to believe that their security measures are mature enough to fend off cyber threats. Their confidence is rooted in a reliance on conventional security paradigms, including the deployment of tools like cloud security posture management (CSPM), application deployment through secure pipelines or the utilisation of native services provided by cloud service providers (CSPs), such as firewalls, network protection, et al. However, the reality of security readiness in the cloud environment is far more complex than is initially perceived.
Enterprise security challenges
When it comes to cyber security in the cloud, a few important questions need to be answered.
- Why do security breaches occur despite organisations diligently implementing stringent security measures?
- Why do organisations struggle to comply with regulations and standards like GDPR, PCI, etc? What aspects have they overlooked in their current approaches to compliance?
- What are the obstacles to effectively mitigating cloud security risks? How can an efficient risk management strategy be developed to address these challenges?
- Why do enterprises often remain reactive in responding to cyber attacks? What steps can they take to transition to proactive threat mitigation?
- Do the current security controls provide comprehensive protection across the entire enterprise landscape? What contributes to gaps in the security posture? How can these gaps be mitigated effectively?
Despite the confidence in their security measures, organisations often find it challenging to address these critical questions. They frequently underestimate the criticality of their security posture until they experience a major breach or fail to comply with regulations.
Enterprise cloud environments are inherently complex, involving the utilisation of multiple cloud accounts, regions, environments, business units, applications, and more. The stakeholders engaged with these cloud environments interact with them using various approaches. The security and operations stakeholders, too, look at security from different perspectives to protect across different layers of the enterprise. This diversity often leads organisations to adopt distributed approaches to security. However, without a unified strategy, managing security across the enterprise becomes increasingly complex. Therefore, a cohesive security governance strategy is indispensable to align these disparate approaches and ensure comprehensive protection against evolving cyber threats.
| Cybersecurity: A few facts |
| Inevitability of cyberattacks: Regardless of an organisation’s size or the maturity of its security, the threat of cyberattacks is inevitable.
Sophisticated attack vectors: Hackers continuously innovate and adapt, often outpacing the capabilities of traditional security defences. Their sophisticated methods and techniques enable them to penetrate even the most secure systems. Flexibility vs security: Defending against these sophisticated threats is a multifaceted challenge. While organisations invest in various security measures, the flexibility of modern IT environments makes it difficult to maintain a comprehensive security posture. Blind spots: Security breaches can go undetected for extended periods, allowing attackers to operate stealthily within an organisation’s network. In many cases, the lack of effective monitoring and detection mechanisms contributes to these gaps. Evolution of security alongside attacks: Cybersecurity is not a one-time investment but an ongoing process of adaptation and improvement. Organisations must consistently evaluate their security stance and adjust their defences to counter evolving threats. |
Gaps in traditional cloud security approaches
Adhering to traditional cloud security approaches across any enterprise cloud security requirement is like fitting the same engine into every vehicle without calibrating it to suit each vehicle’s unique specifications. Just as an engine performs optimally when calibrated to the vehicle it powers, security measures are most effective when customised to meet the diverse needs and challenges specific to the cloud environment.
- Visibility challenges: Cloud environments introduce complexities that obscure security threats, creating blind spots in monitoring and control.
- Lack of unified strategy: Inconsistent security practices across different cloud environments lead to fragmented controls and ineffective measures. Without a unified strategy for hybrid and multi-cloud deployments, organisations struggle to enforce consistent security policies, resulting in gaps in coverage and vulnerability to cyber threats.
- Adaptation and proactivity: Reactive security strategies often overshadow proactive defence mechanisms, leaving organisations exposed to evolving cyber threats.
- Lack of comprehensive controls: Traditional security approaches may not adequately address the diverse and distributed nature of cloud deployments, leaving gaps in security coverage.
- Collaboration and silos: Disjointed efforts and a lack of collaboration among security teams impede effective security practices and coordination.
- Lack of exposure-based prioritisation: Enterprises’ emphasis on redundant security measures over exposure-based prioritisation may leave potential vulnerabilities exposed.
It’s evident that security encompasses multiple aspects, including people, processes, and technology, all of which have inherent gaps. The complexity of the enterprise cloud landscape further exacerbates these challenges, as exploitable loopholes may exist in various security implementations.
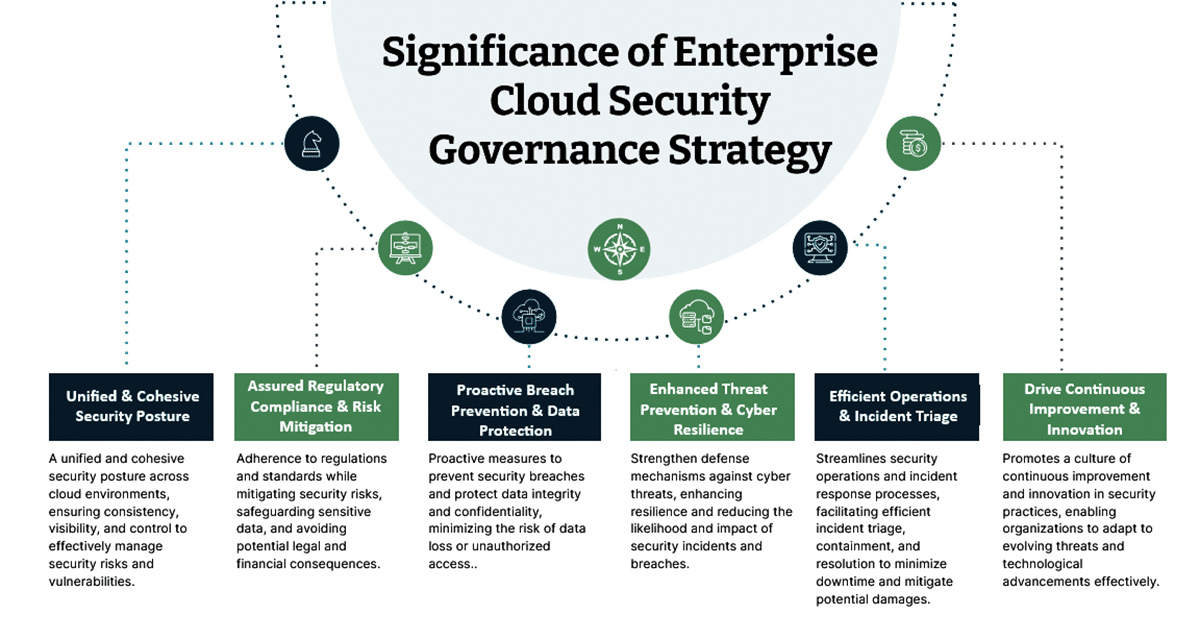
To bridge these security gaps effectively, organisations must adopt holistic enterprise-wide security strategies that proactively address threats, ensure regulatory compliance, and bolster security controls across their enterprise cloud ecosystem. Therefore, implementing an enterprise cloud security governance strategy is essential to effectively address these gaps and ensure comprehensive protection.
Relying solely on native cloud security services and third-party tools may result in overprotected areas alongside under-secured zones in the cloud, leading to a fragmented security posture characterised by redundant and disjointed security measures. Consequently, organisations may be exposed to potential blind spots in the cloud, increasing the risk of security breaches.
To mitigate these risks, it is imperative to adopt comprehensive enterprise cloud security strategies that prioritise threat detection, response capabilities, regulatory compliance, and overall security posture across the entire enterprise IT landscape.
Need for an enterprise cloud security governance strategy
The enterprise cloud security governance strategy is a tailored framework ensuring secure, compliant operation of cloud systems that align with organisational requirements. It employs a proactive and convergent approach, aiming to secure every facet of the enterprise cloud landscape. This strategy encompasses a seamless workflow, establishing baseline security policies to ensure their consistent implementation and operation. It also includes proactive exposure detection and remediation of vulnerabilities, with a focus on incorporating these remediation efforts into the baseline to prevent future occurrences. The goal is to converge security implementation across the enterprise IT landscape, establishing a unified security posture managed by the enterprise security team.
At its core, this governance strategy encompasses policies, procedures, baselines and controls governing the use, management, and protection of cloud resources throughout the organisation. It sets standards for security and regulatory compliance, as well as best practices for cloud adoption and usage. The strategy incorporates mechanisms for risk assessment, monitoring, and incident response to effectively detect and mitigate security threats and vulnerabilities in the cloud environment.
Additionally, the strategy defines clear roles and responsibilities for stakeholders involved in cloud security, promoting continuous security awareness and training initiatives. It fosters collaboration between IT, security, and business units to ensure that cloud security objectives are aligned with organisational goals.
Understanding the distinctions between a ‘cloud security strategy’ and an ‘enterprise cloud security strategy’ is crucial for designing a well-defined security posture across the enterprise. Enterprises must establish clear security objectives and develop comprehensive frameworks that integrate best practices from diverse sources. By aligning cloud-native security services and tools with broader enterprise cloud security goals, organisations can create a robust 360-degree security strategy, addressing gaps across people, processes, and technology.
In the next article, we will explore the nuanced differences between these strategies and approaches, examining their significant impact on designing enterprise-wide cyber resilience.

















































































