Before a software application or a Web application can be released to the public, it has to undergo rigorous testing procedures to ensure its reliability, scalability, durability and its performance under load or stress. This article gives readers an insight into the types of testing required to evaluate the robustness of the software or Web application, and gives an overview of open source tools that can be used for the purpose.
The process of software development integrates the tasks of rigorous testing on multiple parameters and dimensions so that the overall performance of the software suite is good. Software testing is mandatory for every type of software product, whether it is for the desktop, is standalone or a Web based application. Without proper testing, the software application can behave abnormally or can crash when subjected to specific inputs.

Testing strategies for Web applications
Load testing: This is the process of evaluating the behaviour of software being accessed by a large number of users concurrently. The capacity of the software to handle the load of users is analysed.
Stress testing: This analyses the robustness of software. It identifies the specific points at which the software modules incur problems, and evaluates them under extreme conditions of system failure.
Security testing: This discovers the vulnerabilities and security loopholes in the software. It also includes penetration testing, whereby one tries to identify the hacking or cracking probabilities of the software.
Smoke testing: This ensures that important and key features of the software product are working well. It is used to check the stability of software for further stages of testing. The most critical functions are analysed in this testing strategy.
Unit testing: The software is tested at the component and module levels so that the behaviour of individual units can be analysed.
Acceptance testing: The evaluation of software based on the prescribed software requirements specifications (SRS) is done to make it delivery-ready. The levels and scores for the acceptability of the software product are investigated.

Graphical user interface (GUI) testing: The proper functioning of the GUI or simply the front-end of the application is tested to ensure the software is user friendly and able to function as per the requirements.
Gorilla testing: The software modules are tested repeatedly under assorted scenarios and inputs so that their consistency can be checked. This is also referred to as frustrating testing because it involves iterative testing of the same component and the identification of bugs.
Performance testing: This involves evaluating the software product on multiple aspects including speed, load, traffic, stress, susceptibilities and many others.
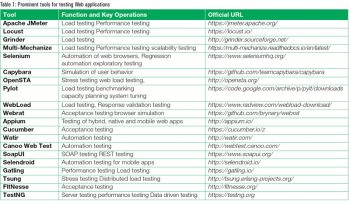
Prominent tools for Web application testing
Table 1 lists open source tools for Web app testing.
URL: https://locust.io/
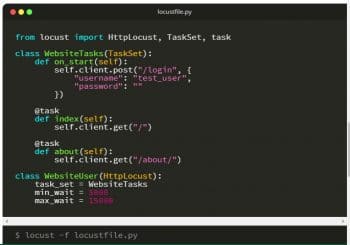
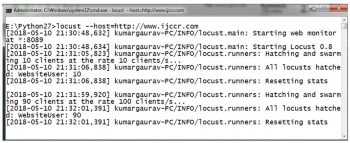
Locust is a Python based tool to evaluate the behaviour of a Web application that is being used by multiple concurrent users. Locust can generate the traffic that connects to the Web application in order to test its behaviour under huge load. It is one of the high performance, free and open source tools for load testing. Locust defines the behaviour and load of virtual traffic on the Web application or server. It creates enormous, swarm based traffic so that a random load can be put on the website.
For example, to test the behaviour of a website with 1000 concurrent users, you might actually need to get those 1000 users, which in reality is practically impossible. Using Locust, any number of users can be generated and a report based on multiple parameters (including the number of requests, content size, failure attempts, etc) is presented.


Locust has plain code without any complex settings. The easiest way to install it is from PyPI, using Pip, as shown below:
> pip install locustio
The code of Python locustfile.py can be directly executed on a command prompt to test the Web application.
The key features of Locust are:
- Free and open source under Apache
- Command line interface (CLI) based
- Evaluates both standalone or live websites
- Conducts performance testing for Web servers
- Specifically for HTTP Web Server
- Load testing and benchmarking
- Platform independent
Apache JMeter
URL: https://jmeter.apache.org
Apache JMeter is another free and open source tool that is used for load testing, performance testing and to gauge the functional behaviour of Web applications. It was developed for the audit of Web applications, but nowadays it is also used for core network functions and the deep evaluation of protocols.
Apache JMeter is able to test and present a deep audit of the following:
- File Transfer Protocol (FTP)
- Directory services
- Lightweight Directory Access Protocol (LDAP)
- Database connections
- TCP
- Mail protocols
- SMTP
- POP
- IMAP
- Web protocols
- HTTP
- HTTPS
- Java objects
- Shell scripts
- Native commands
Apache JMeter is a feature-rich IDE for testing, debugging and recording test plans so that the in-depth analytics of the Web applications can be done. The detailed documentation and tutorials are available on the official website of Apache JMeter, which can be used for assorted case studies.
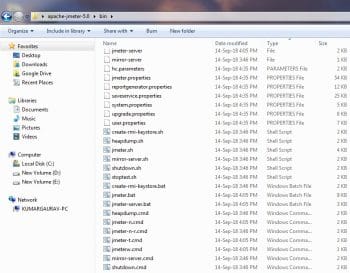
Apache JMeter can be downloaded from http://Apache JMeter.apache.org/download_Apache JMeter.cgi for different platforms and flavours as it is cross-platform software. From this link, Apache JMeter is available in compressed format. It is extracted with the executable files which are available in the bin directory (Figure 4).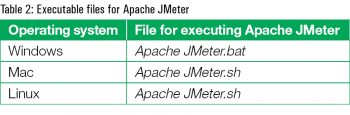
The GUI of Apache JMeter has many features and options for creating and evaluating test plans.
There is no specific naming convention or compulsion regarding the title of a test plan. The testing engineers or audit experts can specify the name or title as per their own preferences (Figure 5).
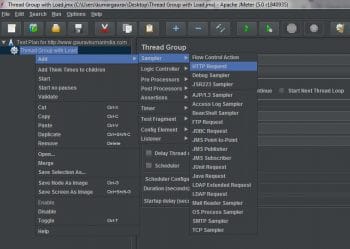
The thread group is used to generate the voluminous traffic that is required for the testing of an application (Figure 6).
A number of users are created virtually without a physical presence so that the Web application can be tested and, thereby, the cumulative performance can be investigated by the Web masters and administrators.

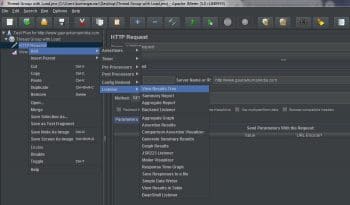
The option of HTTP Request is selected because in the case of Web application testing, the HTTP protocol works to present the outcome on the Web browser or HTTP client. The HTTP client opens the Web page or URL only if that particular link is responding without any issues.
The Web application under testing can be specified in the suite of Apache JMeter in terms of the official link or IP address so that the direct connectivity with the Web server can be evaluated for further investigations (Figure 9).
The option to select ‘View Results Tree’ enables the Web administrator to visualise whether the load testing parameters and factors are successful under assorted and large loads on the Web application (Figure 10).
From the analysis of logs and the response from the server, it can be checked whether the request to the Web application was successful or not (Figure 11). The response code presents the cumulative outcome from the server, right from the initial point of contact by the client.

HTTP Unbearable Load King (HULK) automation for load testing
Generally, penetration testers are dependent on third party tools and software applications for digital forensics and to audit Web applications. This approach of using third party software is not always reliable and secure.
Different testing strategies can be implemented using core programming scripts written in Python. Even though there are many tools and libraries for load testing, stress testing and performance testing, Python programs can be directly used for these tests. Using unreliable tools for penetration and load testing can be dangerous because our own system’s information can be shared to the other locations and will not be secure.
HTTP Unbearable Load King (HULK) is a type of DDoS (distributed denial of service) attack on the server but it can be used for testing Web applications too. By implementing HULK, the performance of a Web application can be tested to check whether it is able to handle the DDoS or HULK based traffic. If the Web application goes down or faces excessive delay in opening, preventive measures can be taken. The HULK script generates an unbearably huge load on the Web application, helping the Web administrator to check whether the application will work fine in real-world scenarios.
Web masters and network administrators can analyse the error log files and access the log files to check the DDoS attempts, and also evaluate the performance of a Web application after carrying out HULK or similar implementations.
Scope for R&D
In the domain of security for Web based applications, there are many perspectives that need to be addressed and worked out. The following are some of the aspects and research points that can be solved by researchers, corporate organisations and academicians in the field of software testing and forensics based audits:
- Biometric integrated access for secured Web portals;
- Development of trust architecture for secured Web applications;
- Integrity-aware vulnerability recognition in Web applications; and
- Deep learning based identification of suspects accessing Web applications without permissions.