In the computer age, data is wealth, but when stored in databases it is prone to various kinds of vulnerabilities like SQL injections, abuse of the DB’s features, broken DBs, data leaks, etc. This article takes a look at the various types of threats to databases and some solutions.
Today, while billions of bytes of data are generated every minute, leading to public cloud computing and the growth of Web 2.0 applications, the relevance of database security becomes all the more paramount. Enterprises are now leveraging open source products for a range of business use cases. Popular open source databases (MySQL, PostgreSQL and MongoDB, to name a few) have seen increased adoption of close to 53 per cent by enterprises, as per statistics. Cost savings, ease of use, avoiding vendor lock-in and community editions are the main reasons for the popularity of open source databases. It is also believed that OSS is more secure because more eyes are looking to find and fix problems. However, security issues need in-depth expertise in this field and not all developers are security experts.
Common attacks to databases and how to address this issue
Databases are an important reservoir of mass information that an enterprise works with. Theft, fraud, loss of privacy, integrity and availability are reasons why data can be compromised. This could be because of deliberate human actions, natural hazards or random events. At the bare minimum, it is required that the database ensures physical and logical integrity. In addition, integrity of each element that makes up the database should be ensured. Access control, user authentication and database availability are other crucial areas that have to be secured. For security hardening, the DBA would need to apply security policies that limit access to data stored on servers.
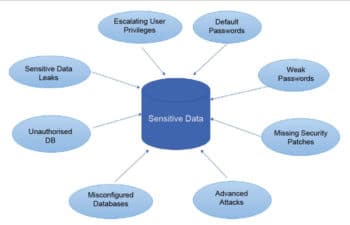
The common threats that databases face can be categorised as follows.
Excessive privileges: If users are granted more privileges than required, those privileges can be used to gain confidential information. Query-level access control should solve the issue.
Privilege abuse: Users may misuse privileges for unauthorised purposes. Access control policies should be in place to mitigate this.
Unauthorised privilege escalation: Attackers may convert low-level access privileges to high-level privileges.
Platform vulnerabilities: The platform or operating system may be vulnerable to leakage and corruption of data. This could be mitigated by an efficient patch management process and vulnerability assessment activities.
SQL injection: This attack makes a user send unauthorised database queries which lead to the server revealing information. This type of threat is addressed by using prepared SQL statements.
Denial of Service: This involves making the resource unavailable for the purpose it was designed. That is, access to data or the application is denied to the user.
Backup exposure: The backup storage media remains unprotected from any attack.
Database security and open source
Most open source databases have security concerns like access controls and inbuilt secure communication — security research and tools are often absent. Third party vendors typically do not port their formalised assessment, monitoring, auditing and masking tools because the demand does not justify the costs.
Tasks such as collecting user permissions, manual comparison of settings in relation to established policies and keeping up to date with patches are very time-consuming and error-prone, and can be automated by open source software developers. Access control and use of SSL are features often provided by vendors, but advanced security such as thwarting SQL injection and memory exploits falls under the developer’s purview. Smaller firms usually have trouble justifying the cost of developing these features.
Comparing a few open source DBs for security
The security vulnerabilities of four open source DBs are compared in the areas of data encryption, client-server communication path encryption and authentication, inter-cluster authentication and encryption, script injection and DDoS attacks.
a) MongoDB: All data is unencrypted and stored as plain text. The MongoDB ports — 27017 and 28017— have no data encryption. In shared mode, MongoDB does not support authentication, which can be activated in standalone mode, though. Attackers can use JavaScript to hack MongoDB.
b) Cassandra: Data files are stored without encryption. The current version of Cassandra uses SSL. However, it is not enabled by default and hence the data in motion would be unencrypted. SQL injections are easily accomplished using the Cassandra Query Language. DDoS attacks can also be easily made since Cassandra runs on one thread per client, and attackers can easily make fake connections and bog down resources.
c) CouchDB: CouchDB does not have automatic data encryption. Client-to-server communications have built-in SSL support. The DB has JSON injection vulnerabilities as it uses JSON to manipulate data. CouchDB is also known to be affected by DDoS attacks.
d) Redis: Redis does not support encryption for data at rest or in motion. Redis is used for caching and hence is designed to function rapidly. Therefore, it does not have many components for its security. It has been reported, though, that Redis is not prone to injection or DDoS attacks.
Security can be enhanced for the above (and other) NoSQL open source databases by encrypting data at the application or OS levels. The use of reverse-proxy would help set up SSL connections for encryption. Handling SQL injections and DDoS attacks requires more effort from developers.
With the shortage of third party tools, the open source software industry is taking on the onus of developing security features for its products. According to the CTO of Ingres, the company has built its own security features with a clearly written guide for distribution. Similarly, Postgres has declared that it has tightened its security focus in the latest releases of the database by including support for RADIUS server authentication and LDAP support. In the coming years, it looks like the OSS industry will focus more on the security for its products and invite support from third party tools.

















































































