Malware is computer software that can lead to serious disasters, ranging from vital data loss to a network security breach. It can infect a client computer or a server by means of data transfer, and only sophisticated antivirus software can scan and detect this in real-time. This article describes various types of malware that can affect computer systems, and how ClamAV can be used to mitigate their effects.
There is a lot of antivirus software available in the market for use, but not all of it is free or open source. One such open source software is Clam AntiVirus (ClamAV), which stands out because of its features and effectiveness. ClamAV was first developed for the UNIX operating system but now is also available for AIX, BSD, HP-UX, Linux, MacOS, OpenVMS, OSF (Tru64) and Solaris.
ClamAV does not include any graphical user interface (GUI); it uses only a command line interface. However, various third party developers have developed a GUI for this antivirus for different platforms. For Linux, the ClamTk GUI is used to work with the ClamAV command line antivirus and it’s also free to use. ClamXAV is another GUI used for MacOS but it’s not free (trialware).
For Windows, various GUI apps have been created, which include Immunet, ClamWin and Clam Sentinel. Immunet is a free cloud-based app that works with ClamAV, and is developed and maintained by Cisco. ClamWin is another free front-end made for Microsoft Windows by ClamWin Pty Ltd. This Windows GUI can make ClamAV do on-demand (user started) scanning, automatic updates, scan scheduling, context menu integration to Explorer, and an add-in for Microsoft Outlook. However, ClamWin does not provide on-access scanning and needs additional software to do that. ClamAV can also be used with Mozilla Firefox using a plugin that works with ClamWin to scan downloaded files. Clam Sentinel is also a free GUI app for Microsoft Windows that works with ClamAV.
It runs in the system tray and can detect any file system changes. It scans the modified files using ClamWin in real-time. It can run on Windows 98/98SE/ME/XP/Vista/7/8 and has a real-time scanner for ClamWin. It also features optional system change messages and proactive heuristic protection. Heuristic analysis is used by many antivirus software to detect unknown viruses using various decision rules and weighing methods. ClamAV, too, uses this type of protection.
ClamAV is mostly used for email scanning and is actually a framework, which provides a protection engine that can be connected to a Message Transfer Agent (MTA) like Sendmail, PostFix, etc. It’s an excellent email gateway AV deployed by ISPs, telecom service providers, and Web hosting companies. It’s also used by many AV gateway vendors like Barracuda and OS vendors like Apple.
Types of malware
Malware is a computer program or software that contains a bug (created intentionally or because of bad coding), which can cause harm or access to a computer system or data, without the consent of the user. Various types of malware include computer viruses, worms, Trojan horses, ransomware, spyware, adware, rogue software, wiper and scareware. Among these malware, computer viruses and Trojan horses are most commonly used to harm a computer, and are spread through Internet files and computer games.
- Computer virus: A virus is malware that can infect a computer file system from any infected file downloaded or saved in that computer. Just like a real biological virus, a computer virus can reside inside a file like an infection. The virus gets activated when that infected file is opened, and then it either changes or damages the data and infects other files in the computer. A virus requires a host file to which it writes its code. That’s why most of the computer viruses can enter a computer though unreliable sources like pirated software and games, email attachments, and file transfers through removable storage drives like a USB flash drive.Elk Cloner, Cascade, Brain, Ghostball and Ping-Pong are examples of computer viruses. Elk Cloner was the first computer virus detected in 1982. It was able to attach itself to the Apple II file system and was spread through floppy disks. With antivirus software becoming more powerful, computer infections are caused more often by worms than by viruses these days. That’s because viruses require a modification of the files in order to replicate but worms don’t, and powerful antivirus software prevents unauthorised access to protected files.
- Worms: As the name suggests, a computer worm program can jump just like a worm from one location to another, but the location can only be a host computer. When a worm invades a computer, it doesn’t infect any file like a virus, but spreads by copying itself from one computer to another through a connected network. After entering a host computer, it starts scanning the network to find any other connected computers (hosts) and when it does so, it transfers itself to them using a recursive method. The main purpose of a worm is to control the host computer or a group of computers connected to a network. Unlike viruses, worms don’t always harm the files stored in the computer but can harm the network by using the bandwidth for controlling the computers.Morris, Mydoom, Here you have, Shamoon and Linux.Darlloz are examples of computer worms. Among these, Morris was the first one to be detected in 1988.Written by Robert Tappan Morris, who was a graduate student at Cornell University, it was launched on November 2, 1988, from computer systems at the Massachusetts Institute of Technology. This led to the first felony conviction in the US under the 1986 Computer Fraud and Abuse Act. Mydoom was another very bad worm attack and caused an estimated damage of US$ 38 billion in 2004. This worm spread through mass emailing. It first infected a computer that opened the infected emails. It then extracted email addresses from this computer and sent emails to them. It was also able to connect other infected computers over the Internet, forming a web of computers called a botnet, which was able to cause Distributed Denial of Service (DDoS) attacks.
- Trojan horse: A Trojan horse is a kind of malware that can deceive the user. That’s why the term is derived from the ancient Greek story of a deceptive Trojan horse that led to the fall of the city of Troy. This type of malware can come with other software as a package, and the user runs the software thinking it is reliable. That’s why most pirated software or games come with such Trojan horse malware, and you can install these without knowing about the malware injected into the files. However, most Trojan horses are spread through social media sites and emails. The attacker sends an email containing a link or attachment with the infected files and the user is duped to click on the link or run the file – which is also known as phishing. That’s why it’s a good practice not to click on any links or open file attachments from unknown senders.Once the Trojan horse is executed by the user unknowingly, it starts running in the background and executes the payload. The payload can be anything, but most often is capable of controlling the user’s computer and stealing information. Trojans may allow an attacker to access a user’s personal information such as banking information, passwords or personal identity, and can also delete a user’s files or infect other devices connected to the network.EGABTR, DarkComet, Blackhole exploit kit, Gh0st RAT and Kedi RAT are some examples of Trojan horses. Among these, EGABTR was detected in the early 1980s. It was actually a graphics utility to improve the EGA display but the Trojan payload would delete the File Allocation Table (FAT) of the hard drive by displaying a message “Arf! Arf! Got you!”. Kedi RAT was a Trojan detected in 2017 and belongs to the Remote Access Trojan (RAT) category. RAT malware can infect a computer and give remote access to a hacker, which means the latter is able to control and access the infected computer from another computer using the connected network. Kedi RAT was distributed in a Spear Phishing Campaign and it targeted Citrix users. This malware was able to evade many malware scanners, and was able to communicate with the control centre (hacker) via Gmail using HTML and HTTP protocols.
- Ransomware: This type of malware causes temporary denial of access to data and threatens the user by demanding a ransom amount. Some ransomware uses cryptoviral extortion techniques to encrypt the user’s files, making it very difficult to access them, and informs the user that it will decrypt the files only after the ransom is paid. The payment is demanded through a cryptocurrency like Bitcoin so that the source of attack is not traceable. Most ransomware is delivered to a computer using a Trojan horse by duping the user to download an infected file or click on a link that activates a Trojan script. However, a worm can also deliver ransomware. For example, the WannaCry worm travelled automatically between computers without user interaction and worked as ransomware.AIDS, CryptoLocker, Locky, WannaCry and Thanatos are examples of ransomware. AIDS was the first ransomware detected in 1989 and was written by Joseph Popp. It was able to hide the file names on the hard drive and displayed a message claiming that the licence to use a certain piece of software had expired. The user was asked to pay a ransom amount of US$ 189 to be paid to the PC Cyborg Corporation, in order to obtain a decrypting tool. Thanatos was another ransomware detected in the year 2018 and was the first to accept ransom payment in Bitcoins. This ransomware was able to encrypt the stored files on the hard drive; it changed the file extension to ‘.THANATOS’ and demanded a ransom amount of 0.1 Bitcoin in order to decrypt the file.
- Spyware: This type of malware acts as a spy and gathers information about the user and the data stored in the computer. The gathered information is sent to the spyware developer and the infected computer is kept under surveillance. Such spyware can come from an unreliable third party software or even through a legitimate app. Some trusted websites can also run spyware when users visit them to keep track of them. The purpose of spyware can vary from advertising to hacking, and that’s why it’s difficult to determine whether spyware can be harmful or not.Reader Rabbit, Internet Optimizer, CoolWebSearch, SpyEye and Go Keyboard are a few examples of spyware. Among these, Reader Rabbit was the first spyware detected in the year 2000 by ZoneAlarm – a firewall/antivirus software developed and maintained by Zone Labs. Reader Rabbit was educational software developed and marketed by the Mattel toy company. But this software was working as spyware and transmitted the user’s information back to Mattel. The Go Keyboard app available in the Google Play store also works as spyware and transmits personal information to remote servers without the explicit consent of the user. This information includes the user’s Google account email, language, IMSI, location, network type, Android version and build, and the device’s model and screen size. However, the developers of this app – a Chinese company called GOMO Dev Team — claim in the app’s description that they will never collect personal data including credit card information.
- Adware: This type of malware doesn’t do any harm to the data, but it displays advertisements to users through the user interface (UI). The purpose of this malware is to generate revenue for the developer in two ways – through the display of the advertisement and through ‘pay-per-click’, where revenue is generated based on the number of clicks by users on the displayed advertisement. Adware often comes with freeware (free to use apps) and this is the most common reason for a developer to offer an app for free. In the Google Play store, most of the free apps and games come with adware, and that’s how both Google and the developer generate revenue. The most common problems from adware are frequent system crashes and slow Internet speed.
- Rogue security software: This is a kind of malware that displays a false virus alert to the user and asks for the purchase of a virus removal tool. This type of malware falls between scareware (malware that scares the user) and ransomware. In 2005, SpySheriff rogue security software misled users with a false security alert and scared them to buy the software.
- Wiper: This type of malware is intended to wipe the hard drive of the user’s computer. The attack on Sony Pictures in 2014 was done by a hacker group, which used a variant of the Shamoon wiper malware to erase the company’s computer infrastructure.
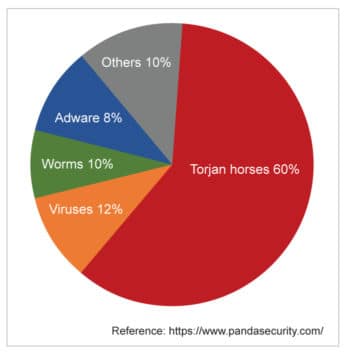
- Scareware: This unique malware is intended to only scare the user by displaying false security alerts. However, some scareware can work as ransomware and demand the purchase of a tool that can resolve the security issue. Most scareware reaches users through social engineering and many untrusted websites can run scareware script also. In 2005, Microsoft and Washington State successfully sued Secure Computer (makers of Spyware Cleaner) for US$ 1 million over charges of using scareware pop-ups.According to one report from Panda Security (a Spanish cybersecurity software company), the prevalence of malware by category is 60 per cent Trojans, 12 per cent viruses, 10 per cent worms, 8 per cent adware, and 10 per cent others.
The techniques used by antivirus or anti-malware software
Malware may be of various types and could give many kinds of problems. To get rid of any such malware, we need powerful antivirus software. An antivirus or anti-malware is software that is capable of preventing and detecting a malware, but may not always be able to remove it. It was first developed to detect only computer viruses because these were the more common types of malware attacks initially. That’s how it got the name ‘antivirus’. But nowadays, such antivirus software is also capable of dealing with many kinds of malware; so now such software can also be termed as anti-malware. Reaper was the first antivirus program created by Ray Tomlinson in 1972 and was capable of deleting the Creeper virus.
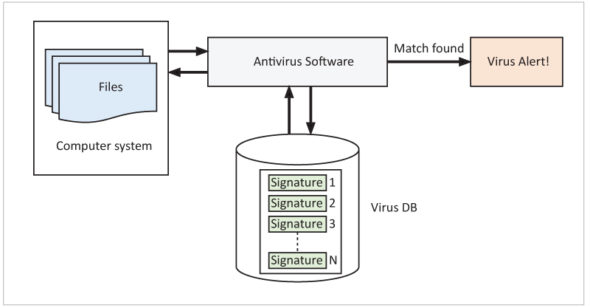
Antivirus software works mainly using signature and behavioural based techniques. In signature based detection, when any new malware is discovered by researchers, its file signature is extracted and added to the database of the antivirus. During a security scan, the antivirus checks for similar signatures in the files it scans, and if any match is found then it’s detected as malware. In behavioural detection, the algorithm or the intention of a malicious program is understood and all suspicious behaviour is added to the database of the antivirus. During the execution of a file, the antivirus monitors the executed program and tries to find behaviour that matches with the database. If any match is found, it’s detected as malware. Besides these two techniques, other methods like sandbox detection, data mining techniques, heuristic analysis, rootkit detection and real-time protection are also used.
Sandboxing uses a virtual environment to run the suspected program and isolate it from the real environment. It then checks the behaviour of the program and compares it with the database; if any match is found, it is flagged as malware. This method is safe and protects the system from any malware attack.
The data mining technique uses machine learning algorithms to classify malware based on its behaviour.
Heuristic analysis is a technique used to identify the genre of a virus or malware. Usually, attackers can create variants of a virus and there can be a family of similar viruses, forming a genre. It is easier to identify the signature of the genre than to detect a specific virus. Heuristic analysis creates the signature genre of various families of viruses based on their behaviour, which is stored in the database of the antivirus. When the behaviour of a program matches the genre of a virus, it is flagged as a virus belonging to that family.
Rootkit detection is used particularly for malware called rootkit, which can take administrative control over the computer. A rootkit can tamper with the antivirus, disabling it, and is also sometimes very difficult to remove. A real-time antivirus scans each and every process executed in the background in real time. This protection is very important and prevents unwanted malware from being activated.
Whatever technique is used by the antivirus software, the most challenging thing is the prevention of any false positive detection. Many programs may behave like malware or carry a file signature that looks like malware, but never do any harm. But many antivirus or anti-malware software sometimes detect such programs as malware.
For example, here is a C program using the printf() function:
#include <stdio.h>
main()
{
int n;
n=1;
while (n>0)
{
printf(“Enter a number: “);
scanf(“ %d”,&n);
printf(“The number you entered is: %d\n”, n);
}
}
The above code will be detected as malware by some antivirus when compiled. But when that code is written using only the puts() function instead of printf(), it is not detected as malware.
The following code is written by replacing printf() with puts():
#include <stdio.h>
main()
{
int n;
n=1;
while (n>0)
{
puts(“Enter a number: “);
scanf(“ %d”,&n);
puts(“The number you entered is: %d\n”, n);
}
}
The above code can be compiled and run without any malware detection. This is because printf() has uncontrolled format string security risk, and it’s possible to carry a malicious act of printing data from the call stack or possibly other locations in memory using format tokens like %s and %x. One can also command printf() to write arbitrary data to any location using the %n format token, and also write the number of bytes formatted to an address stored on the stack.
Pros and cons of ClamAV
| Pros | Cons |
| • Compatible with major operating systems like Windows, Linux, or macOS, etc. | • Limited functionality and focuses mainly on mail gateway protection. |
| • It has an open source virus database and can be used for research or improvement purposes. | • No support service. |
| • Mail gateway scan is possible. | • Not simple to use and needs various configurations with a command line utility. |
| • Multi-threaded virtual scanner against malware. | |
| • The utility command line allows easy navigation. | |
| • This antivirus is free and any custom GUI front-end can be connected to it. |
Even though ClamAV is a powerful protection engine and uses various techniques for malware detection, the false positive is always a concern for the user. However, some antivirus testing companies have tested and found it to be good. The Shadowserver Foundation (a non-profit security organisation) tested ClamAV for six months in 2011 and found that it was able to detect 75.45 per cent of viruses, putting it in fifth place behind AhnLab, Avira, BitDefender and Avast. AhnLab, the top antivirus, detected 80.28 per cent of viruses. Another antivirus testing company called bestantiviruspro.org reviewed and gave a 5 star (value for money) rating with a score of 72 per cent to ClamAV in 2021, when compared with other commercial antiviruses like Comodo, Windows Defender, Eset and Sophos.
ClamAV architecture
ClamAV works mainly with a virus detection service, virus database and the freshclam tool. The freshclam tool helps ClamAV to update its database, and it can be configured using the freshclam.conf file. This tool can be configured to work either in interactive (on demand from command line) mode or daemon (silently in the background) mode. It supports scripted updates (instead of transferring the whole CVD file at each update, it only transfers the differences between the latest and the current database via a special script), database version checks through DNS, proxy servers (with authentication), digital signatures and various error scenarios.
The virus database is updated from the link http://database.clamav.net by downloading the .cvd files, and the updates can be automated by configuring the freshclam tool. The virus detection service is connected to the virus database along with the protection engine of ClamAV. Various GUI apps like WinClam and ClamTk can be used with the detection engine, but by default, ClamAV can be used with the help of a command line utility also.
The installation and configuration documents of ClamAV can be found at https://www.clamav.net/documents and you can also get community support for ClamAV at https://stackoverflow.com.
Features of ClamAV
The features of ClamAV include:
- A command line scanner.
- Milter interface for Sendmail.
- An advanced database updater, with support for scripted updates and digital signatures.
- The virus database gets updated multiple times in a day.
Built-in support for all standard mail file formats. - Built-in support for various archive formats, including Zip, RAR, Dmg, Tar, Gzip, Bzip2, OLE2, Cabinet, CHM, BinHex, SIS, and others.
- Built-in support for ELF executables and portable executable files packed with UPX, FSG, Petite, NsPack, wwpack32, MEW, Upack and obfuscated with SUE, Y0da Cryptor, and others.
- Built-in support for popular document formats including MS Office and MacOffice files, HTML, Flash, RTF and PDF.
An antivirus is a crucial part of a computer, without which it can be at the risk of malware infection. Using the right antivirus software will keep the computer safe from any malware attack and also protect vital data. However, not all antivirus software are helpful and choosing the right one is important. ClamAV could be the right one for you!

















































































