Online anonymity is quite popular these days for varied reasons. While it gives a voice to the voiceless, it also offers a playing field to mischief makers. This article is a short tutorial on how to go anonymous on the Internet.
To access contents that are otherwise not available due to geographic limitations, netizens are using anonymity. To be anonymous on the Internet means that your IP address is not directly revealed to the host of the content provider, and the request from your browser is routed via proxies. This way the IP address of the proxy system is provided to the content provider, which can be in any geographic location. A number of VPN services have cropped up to help with this. Some are expensive, while some are cheap. The countries for which they provide the proxy differ, and so do the charges. One way to achieve anonymity is by using Tor connections.
Tor connections do have a bad reputation, but are not necessarily so. Internet users may want to browse the Web anonymously without allowing their government, ISP, or even the website they are browsing to view their IP address or browsing habits.
Now let’s see how to create a proxy system to go anonymous on the Internet.
Prerequisites
To create a Tor proxy server of our own, all we need is a UNIX or UNIX-like system. It can be an old PC or laptop, or RaspberryPi zero with the capability of running any lightweight Linux distro and two network connectivity options for the WAN and LAN.
Once you have a running system with any Linux OS installed on it, you can go ahead with the installation of a Tor server. I am using Debian based Linux. The command and process will work only on a similar Linux distro.
If you prefer any other distros, you will need to modify the commands accordingly. Open the terminal and update the system with the following commands:
$ sudo apt-get update $ sudo apt-get upgrade
Now we have to install the Tor server, as follows:
$ sudo apt-getinstall tor
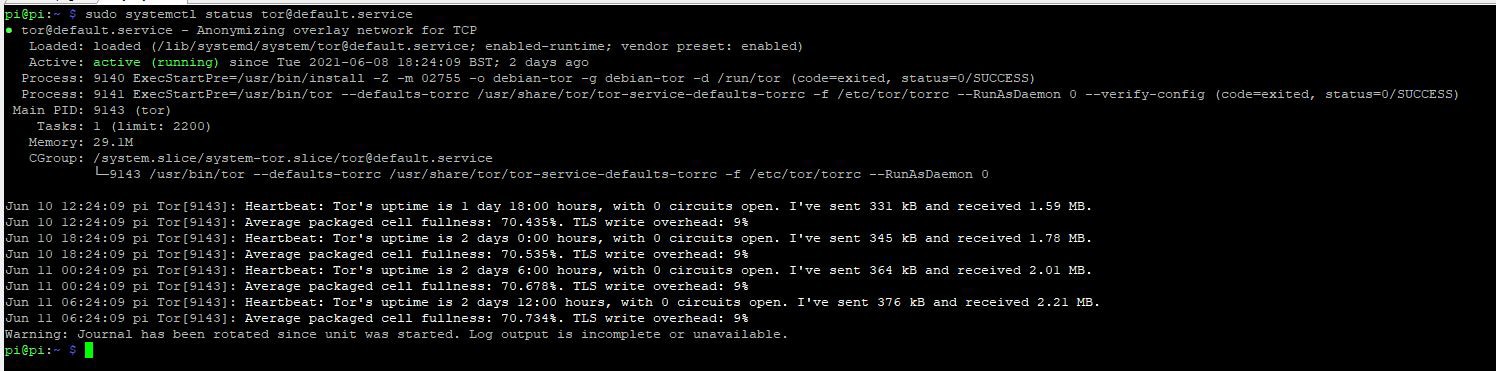
Once the installation is successfully completed, we need to test if the service is running:
$ sudo systemctl status tor@default.service
The output of the above command will be as shown in Figure 1.
Configuration
Since the server is up and running now, it’s time for some tweaks to make the service accessible from other machines. To start with, we have to make some changes in the file /etc/tor/torrc. But before making any change, create a backup of the original file. Open the file in any text editor:
$ sudo cp /etc/tor/torrc /etc/tor/torrc.backup $ sudo nano /etc/tor/torrc
To make the service available on Port 9050 and accept connections from the LAN, include the following lines at the end of the file, assuming the IP address of the machine is 192.168.1.100. (It may be different for you as it depends on your network environment.)
SocksPort 192.168.1.100:9050 SocksPolicy accept 192.168.1.0/24 RunAsDaemon 1 DataDirectory /var/lib/tor
Save and close the file using ctl+o and ctl+x. Restart the service to make the changes effective:
$ sudo systemctl restart tor@default.service
Using the Tor server
Now that we are done with the configuration and setting up of the Tor proxy server, we need to configure our browsers in the other machines in order to access the service and be anonymous. To start with, we have to open the network settings. As an example, for the Mozilla Firefox browser, we can open Settings, and then click on Network Settings at the bottom. We will be redirected to a page where we will see the No Proxy option has been selected by default. We need to change that to Manual Proxy Configuration. In the SOCKS Host, we have to put the IP address of the machine where we have installed the Tor server. In my case, it’s 192.168.1.100. In the adjacent port field, we have to add the port of the Tor service, 9050.
You are all set now, and it’s time to go anonymous and enjoy your own setup.
To test your work, visit www.dnsleaktest.com and check the IP address it shows, which should be the IP exposed to the target websites instead of your original IP.
Choose the proxy country
We will now be able route our traffic through a random IP provided by the Tor service. However, we may need to use the IP of a particular country to access some content, in which case we need to make a few more changes to the file /etc/tor/torrc, which we have already altered earlier above. A word of caution: before you use Tor, be aware of any limitations imposed on using it by your organisation or the country you live in.