Kali Linux is a popular distribution of Linux, most famously used in the field of cybersecurity. This article is about vulnerability testing using Kali Linux. We go through how to install the uniscan vulnerability scanner, and then test the vulnerabilities of a website using this tool.
Vulnerability testing is basically a software approach to test a system and evaluate the risks that are there in the system function, in order to take measures to mitigate and prevent these from actually happening. Now let us get started.
Most of us may be using other distributions of Linux. So, if you want to use Kali, you can download the publicly available .iso files, and install it onto your virtual machine or the computer. I have installed it on a VMware virtual machine for the purpose of this article.
Installation is a pretty straightforward process and you can figure that out. Once that is done, your virtual machine will work as a fully functional Kali Linux system that you can explore, learn and get the experience of using, before you switch to it full-time, in case you want to.
Now, let us get started with the first tool, which is uniscan. Uniscan is a simple Remote File Include, Local File Include and Remote Command Execution vulnerability scanner. You can first update your repo using the following command:
sudo apt update
You can use the following command to install uniscan on your system, as shown in Figure 1:
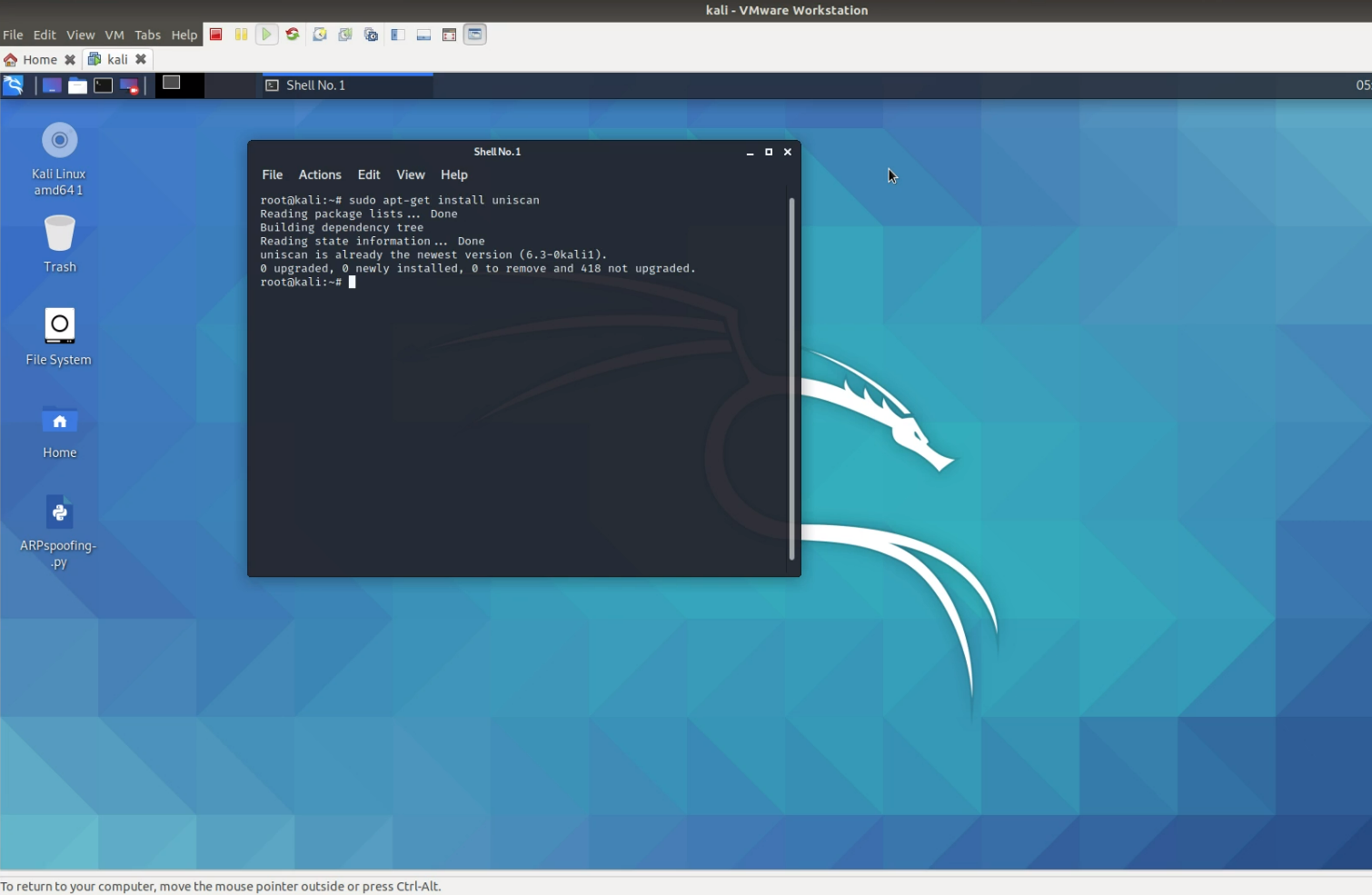
sudo apt-get install uniscan
Then you can check all the options of vulnerability analysis available in the uniscan tool using the following command, as shown in Figure 2:
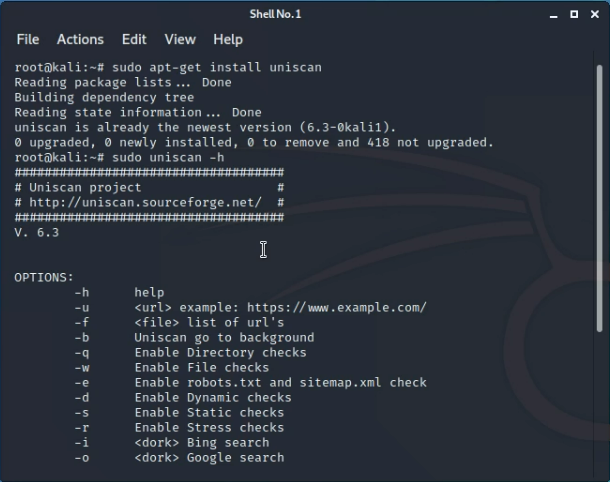
sudo uniscan -h
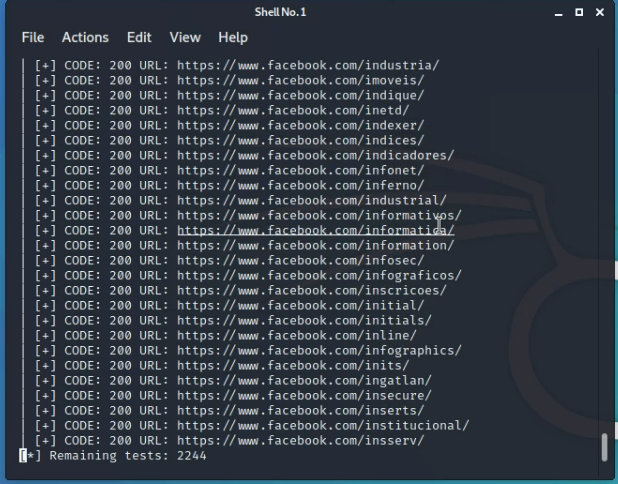
The first option we are going to explore is the -U argument; so the command will be:
sudo uniscan -U https://testphp.vulnweb.com
https://testphp.vulnweb.com is a website that has given permission to test its vulnerability for the purpose of learning. So using the above command we can test the vulnerability and generate a report, which will give us the IP address and we will get to know all the vulnerability details.
Using the above command, uniscan can run thousands of tests on the website, the different folders, sub-URLs, etc, and give us an update. It will crawl through all the folders and give us a full-fledged report, as shown in Figure 3.
This is just some major testing that we can do with the help of the uniscan tool; there are a lot more options that you can explore. Do look at the documentation of the tool and have more fun!!

















































































