A hacker is a highly skilled computer operator who uses bugs and exploits to break into computer systems and networks. An ethical hacker, on the other hand, identifies vulnerabilities in computer systems and networks, and plugs these holes. Here’s a round-up of the ten best operating systems for ethical hackers and penetration testers.
Hacking has been part of computing for over five decades and is a very broad area, covering a range of tasks. The term hacker originated in 1960 at MIT. Hacking is regarded as a process of locating all possible back doors that exist in a computer system or network and, finally, intruding into it. In simple terms, it is regarded as an unauthorised activity to gain access to a computer system or network, to harm it or prevent its normal functions and to steal sensitive information available on computing systems.
On the other hand, hacking can also be a legal activity when it is used to discover back doors and weaknesses in computer systems in order to patch them. This is called ethical hacking.
In today’s cyber world, lots of varied attacks occur every hour and are achieved by professional hackers, virus writers and crackers. The most basic tool required by every hacker is a hacking operating system. Usually, the operating systems specialising in hacking are based on the Linux kernel. These operating systems are regarded as advanced working systems, which include lots of ethical hacking and penetration testing tools.
In this article, the ten best operating systems used by ethical hackers and penetration testers are featured. All of them are free, open source, are based on the Linux kernel and are bundled with many hacking tools.
1. Kali Linux
Kali Linux is based on the Debian-Linux distribution, and is especially designed for digital forensics and penetration testing. It is maintained and updated on a regular basis by Offensive Security Ltd, under the leadership of Mati Aharoni, Devon Kearns and Raphael Hertzog who are core developers. Kali comes pre-installed with more than 300 penetration testing programs and can be installed as a primary operating system on the hard disk, live CD/USB and can even run as a virtual machine using some virtualisation software.
Kali Linux supports both 32-bit and 64-bit images for use with x86 machines, and even supports various development boards like Raspberry Pi, BeagleBone, Odroid, CuBox, etc.

Tool categories
- Information gathering: These tools are used to gather information regarding DNS, IDS/IPS, network scanning, operating system, routing, SSL, SMB, VPN, VOPI, SNMP, email and VPN.
- Vulnerability assessment: These tools access the CISCO network and discover vulnerabilities in several database servers.
- Web applications: These tools are related to Web applications like content management systems, database exploitation, application proxies, Web vulnerability scanners, etc.
- Password attacks: These tools perform password attacks via brute force, dictionary attacks, etc.
- Exploitation tools: These exploit vulnerabilities in target systems for networks, the Web and databases, and to perform social engineering attacks.
- Sniffing and spoofing: These tools sniff the network and Web traffic.
- Maintaining access: These tools maintain access to the target machine, to assess operating system back doors and for tunnelling.
- Reporting tools: These document the penetration testing process.
- System services: These tools contain various pen-testing services like Apache, MySQL, SSH and Metasploit services.
Kali Linux is bundled with several tools that perform wireless attacks, reverse engineering, stress testing, hardware hacking and forensics.
Key features:
- Bundled with more than 600 penetration testing tools as compared to Backtrack OS.
- Completely free and open source and committed to GitHub, with the source code of each package being available.
- Kali Linux is FHS (Filesystem Hierarchy Standard) compliant to locate binaries, and support files and libraries.
- Kali Linux offers a custom kernel for customised coding and patching up the latest updates.
- Every package in it is GPG signed and, hence, committed to high quality standards by developers.
- ARMEL and ARMHF support allows Kali Linux to be installed on various other devices like Pi, Odroid, Chromebook, etc.
Latest version: Kali Linux 2016.2 (32-bit/64-bit)
2. BackBox
BackBox is an Ubuntu-based Linux distribution aimed at assisting ethical hackers and penetration testers in security assessments. BackBox OS is designed with the objective of being faster, easily operable and having a minimal desktop environment. The key advantage of BackBox is that its own software repositories are updated at regular intervals to keep the distribution stable and popular for real-world operations.
The BackBox distribution consists of more than 70 tools for tasks ranging from Web analysis and network analysis to stress testing, sniffing, vulnerability assessment, forensics and exploitation.
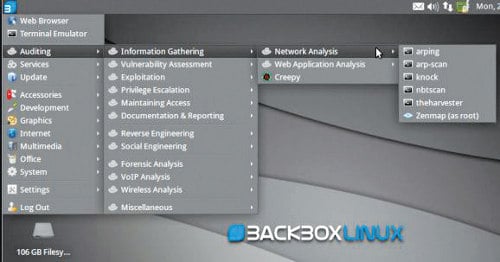
Key features:
- BackBox Linux is one of the first platforms supporting the cloud for penetration testing.
- It is fully automated and non-intrusive, with no agents or network configuration changes required to achieve regular automated configuration backups.
- Saves time and eliminates the requirement of tracking individual network devices.
- With support of the XFCE desktop, BackBox is regarded as fast in operations and suitable even for old configuration systems.
- Completely hacker friendly due to the support it receives for creating its own Launchpad PPA and sending the package to developers who, in turn, contribute instantly to BackBox Linux.
Latest version: 4.7
3. Parrot Security Operating System
Parrot Security OS is based on Debian GNU/Linux combined with the Frozenbox OS and Kali Linux to provide ethical hackers the best-in-class experience of penetration and security testing in real-world environments. It is also designed to provide vulnerability assessment and mitigation, computer forensics and anonymous Web browsing, by the Frozenbox team.
Parrot Security OS makes use of Kali repositories for all sorts of package updates and to integrate new tools. It makes use of the MATE desktop environment using the LightDM display manager to provide an easy-to-use GUI and lightweight environment for computer system analysts to perform all sorts of forensics, vulnerability assessment and cryptography. This OS is known for being highly customisable and for its strong community support.

Key features:
- Equipped with the highly customisable kernel version 4.5, it is currently under rolling release upgrade line and based on Debian 9.
- Has custom anti-forensic tools, interfaces for GPG, Cryptsetup, and support for LUKS, Truecrypt and VeraCrypt.
- It supports FALCON 1.0 programming language, multiple compilers, debuggers and the Qt5 and .NET/mono frameworks.
- Supports Anonsurf including anonymisation of the entire OS, TOR, I2P anonymous networks and beyond.
- A special edition of Parrot Cloud, designed for servers, comprises lightweight Parrot OS distributions without graphics, wireless and forensics tools, and acts as a VPS or dedicated server with only useful security tools.
Latest version: 3.3
4. DEFT Linux
DEFT (Digital Evidence and Forensics Toolkit) is based on GNU Linux and DART (Digital Advanced Response Toolkit), a forensics system comprising some of the best tools for forensics and incident response. DEFT Linux is especially designed for carrying out forensics tasks and runs live on systems without tampering with the hard disk or any other storage media. It consists of more than 100 highly-rated forensics and hacking tools.
It is currently developed and maintained by Stefano Fratepietro along with other developers, and is available free of charge. It is used actively by ethical hackers, pen testers, government officers, IT auditors and even the military for carrying out various forensics based systems analysis.
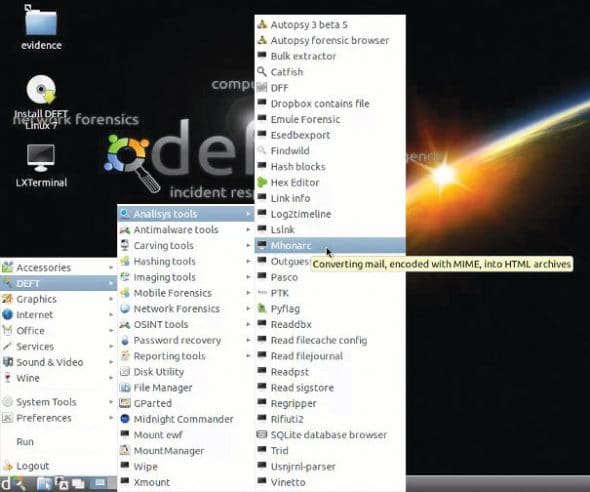
Key features:
- It is based on the Lubuntu distribution comprising open source digital forensics and penetration testing tools.
- Full support for Bitlocker encrypted disks, Android and iOS 7.1 logical acquisitions.
- Consists of Digital Forensics Framework 1.3.
Latest version: 8.2
5. Samurai Web Testing Framework
Samurai Web Testing Framework primarily focuses on testing the security of Web applications and comprises lots of Web assessment and exploitation tools. The credit for developing the Samurai Web Testing Framework goes to Kevin Johnson, Justin Searle and Frank DiMaggio. The Samurai Framework provides ethical hackers and pen testers with a live Linux environment that is preconfigured to run as a virtual machine to perform Web penetration testing.
The Samurai Web Testing Framework includes popular testing tools like Fierce Domain Scanner and Maltego for Reconnaissance, WebScarab and Ratproxy for mapping, w3af and Burp for discovery, and BeEF and AJAXShell for exploitation.
The framework is based on Ubuntu 9.04, is fully open source and receives regular updates with regard to products.
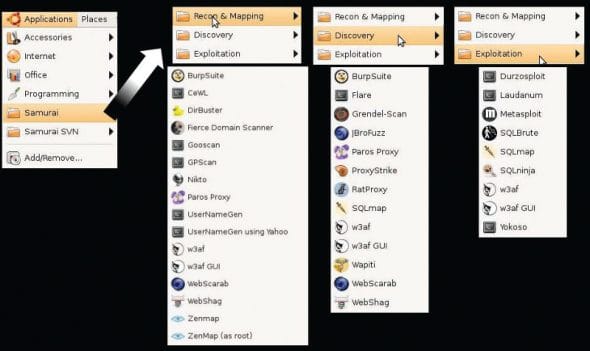
Key features:
- Contains many tools for reconnaissance, mapping, discovery and exploitation, especially focusing on Web penetration testing.
- Equipped with SVN to provide updated security tools, and syncs with active development tools.
Latest version: 3.3.2
6. Network Security Toolkit
The Network Security Toolkit (NST), based on Fedora, is a live bootable DVD/USB Flash drive consisting of the top 125 open source security tools provided by insecure.org to perform network security, penetration testing, network diagnostics and monitoring of day-to-day tasks. The main objective behind the development of NST is to provide network/systems administrators a combined set of open source security tools to carry out operations like network traffic analysis, intrusion detection, network scanning and security patching.
NST has been developed by Ronald W. Henderson and Paul Blankenbaker. It provides a Web interface known as NST WUI and all the tools can be accessed via the Web page. NST is equipped with intelligent package management capabilities based on Fedora and maintains its own repositories of additional packages.
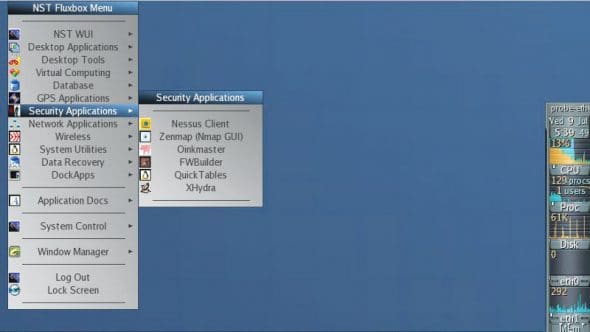
Key features:
- Provides visualisation of ntopng, ntop, Wireshark, traceroute, NetFlow and Kismet data.
- JavaScript console with built-in object library helps in the development of dynamic Web pages.
- Other features include network intrusion detection, Web-based Snort IDS integration, active connections monitor, VNC/RDP desktop session management, host/IPv4 address geolocation and network segment ARP scanner.
Latest version: 24-7977 Release.
7. BlackArch Linux
BlackArch is an Arch Linux-based security and penetration testing distribution, which consists of more than 1600 tools and is regarded as the first choice distribution among security researchers to do Web and applications based security testing. It is a strong alternative to Kali Linux and Backbox in terms of the variety of its tools and ease of use.
BlackArch is basically a lightweight extension to Arch Linux for security researchers, as the tool set within the former is distributed as the Arch Linux unofficial user repository and can even be installed on top of existing Arch Linux.
Arch Linux can be installed on 32-bit and 64-bit machines including ARM based development boards like Raspberry Pi, BeagleBone, etc.

Key features:
- GUI interface is powered by Fluxbox and includes i3, WMii, Spectrwm, Awesome, dwm and Openbox window managers.
- Has modular package groups.
- Installation can be performed from source.
Latest version: 2016.12.29
8. Cyborg Hawk Linux
Cyborg Hawk Linux is regarded as the most advanced, powerful and well-managed Ubuntu based penetration testing Linux distribution created by Ztrela Knowledge Solutions Pvt Ltd. The distribution consists of more than 700 tools dedicated to penetration testing, and more than 300 tools for mobile security and malware analysis.
Cyborg Hawk Linux is completely open source and free to use, and the latest version comes with its own repository. The distribution is highly reliable and stable in the eyes of ethical hackers and pen testers for real-world stress testing of networks, malware analysis and finding out back doors.

Key features:
- Full support for wireless devices.
- Can be installed as a virtual machine.
- Managed and well-sorted menus in the distribution.
- Bundles tools for exploitation, stress testing, reverse engineering, forensics, mobile security and wireless security.
- Secured and well patched kernel.
- Has full capability to run as Live OS.
Latest version: Version 1.1
9. GnackTrack
GnackTrack is an Ubuntu based penetration testing Linux distribution which includes lots of utilities for penetration testing. It has a GUI based GNOME desktop for easy interfacing. GnackTrack is an open source and free project, and contains various significant penetration testing tools like Metaspoilt, Armitage, wa3f and many more.

Key features:
- Supports both 32-bit and 64-bit hardware platforms for installation and running live OSs.
- Standard boot menu for booting up live DVD OS.
- Inspired by Backtrack and the most useful choice for starters to learn and research penetration testing.
Latest version: Version R6
10. NodeZero
NodeZero is an open source Ubuntu based penetration testing Linux distro, which makes use of Ubuntu repositories for updates. It consists of more than 300 penetration testing tools as well as a set of basic services that are required for carrying out all sorts of operations. The Linux distribution is available for download as a dual-arch live DVD ISO image, and can run on both 32-bit and 64-bit computing architectures.
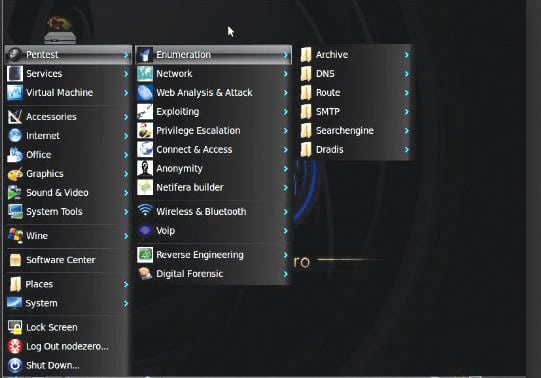
The live OS supports various other features like system memory diagnostic tests, hard disk booting, install direct, safe mode booting, text mode or debug mode.

















































































Come on, if you know the term hacker started at MIT in the 60s you know your definition of hacker is inaccurate. I know words change meaning across time, but to equate a hacker and a cracker is a disservice to the community.
I have read your whole post and I would love to tell you that article is very interesting & thoughtful. I totally agree with your point “hacking can also be a legal activity when it is used to discover backdoors and weaknesses in computer systems in order to patch them”
There so many institutes but as per my knowledge, Koenig Solutions is the great place to learn new things in hacking.
The best hacker and penetration tester I know for blackhat services https://uploads.disquscdn.com/images/56b6095e408693a71494cabd0f2c94866928c24202cc5822b938acdd712d92c1.png
This guy is really good. He hacked into a database for me once. crazy dude