Monthly Archives: February 2012
Developing Apps on Qt, Part 2
In the previous article in this series we went over the installation and some basic examples of Qt. In this article, we will learn...
UEFI: Should Linux Users be Worried?
Microsoft intends to capture UEFI and make GNU/Linux and other free OSs "unauthorised"! Is this true, and if so, what is the community doing...
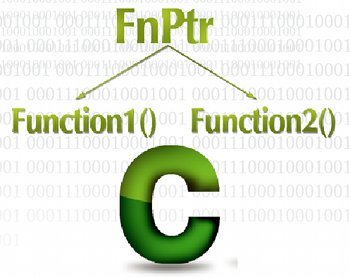
Function Pointers and Callbacks in C – An Odyssey
Function pointers are among the most powerful tools in C, but are a bit of a pain during the initial stages of learning. This...
Device Drivers, Part 15: Disk on RAM — Playing with Block Drivers
This article, which is part of the series on Linux device drivers, experiments with a dummy hard disk on RAM to demonstrate how block...
Building Image Processing Embedded Systems using Python, Part 2
The second part of this article discusses how to use the OpenCV library via the Python interface to perform image processing-based tasks. The previous...
TrueCrypt — Learn the Art of Encryption
When did you last feel that you ought to have secured that important file so nobody else could view it without your permission? Ever...
Open Source Sets Microsoft’s Kinect Free
This first article in this series gives a brief overview of the Kinect sensor, the different terms used like natural user interface and machine...
Guard Your Network with IPCop, Part 3: Block Outgoing Traffic
The first article in the series discussed IPCop 1.4.21, its basic installation and configuration. Though an excellent firewall distro, basic IPCop has limited functionality....
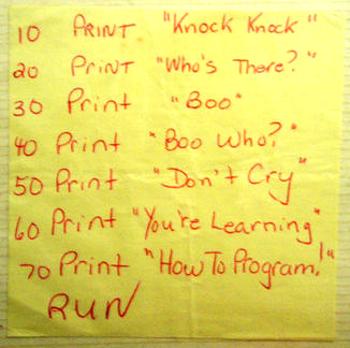
CodeSport
This month's column is special, in honour of LFY's 9th anniversary. We feature tips on how to prepare for programming interviews.
This month, we celebrate...
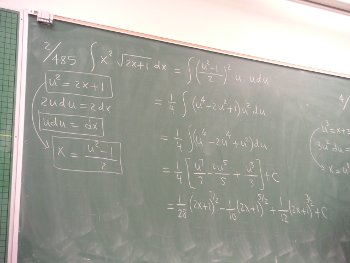
Joy of Programming: Liskov’s Substitution Principle
LSP is a cardinal rule to follow in object-oriented designs. In this column, we'll introduce LSP to those new to OOP (Object Oriented Programming),...