Monthly Archives: February 2012
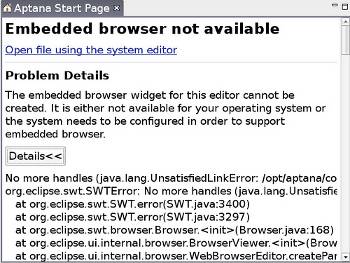
FOSS is __FUN__: The Best IDE
In any forum that talks about programming, a frequent topic is, "What is the best IDE for the language/framework under discussion?" This often leads to...
Exploring Software: Easier Healthcare Using IT
This article is not so much about trying out any software as about the need we all feel for reliable care-givers for the elderly...
Hackers and the Open Source Revolution
This piece corrects the confusion created by mainstream media between "hacker" and "cracker". It also considers the history, nature, attributes, ethics and attire of...
Top 10 Security Assessment Tools
Modern data centres deploy firewalls and managed networking components, but still feel insecure because of crackers. Hence, there is a crucial need for tools...
Cyber Attacks Explained: DNS Invasions
We often read about defaced websites whose pages get changed to some malicious content. How do hackers do it and how do we protect...
Protecode: Software License Management is Like Any Other Quality Management Process
Someone rightly observed: "All code is guilty, until proven innocent." Ask the members of any software development team, and they will agree that tracking...
WordPress on Nginx, Part 2: vhost, MySQL & APC Configurations
Last time around we made our Debian VPS ready with the LEMP recipe. Let's now configure the stack and migrate over the old WP...
WordPress on Nginx, Part 1: Preparing VPS the Debian Way
In this first part, we deal with the LEMP (Linux, Nginx, MySQL, PHP) stack recipe and set up the basic server after installing the...