Monthly Archives: August 2015
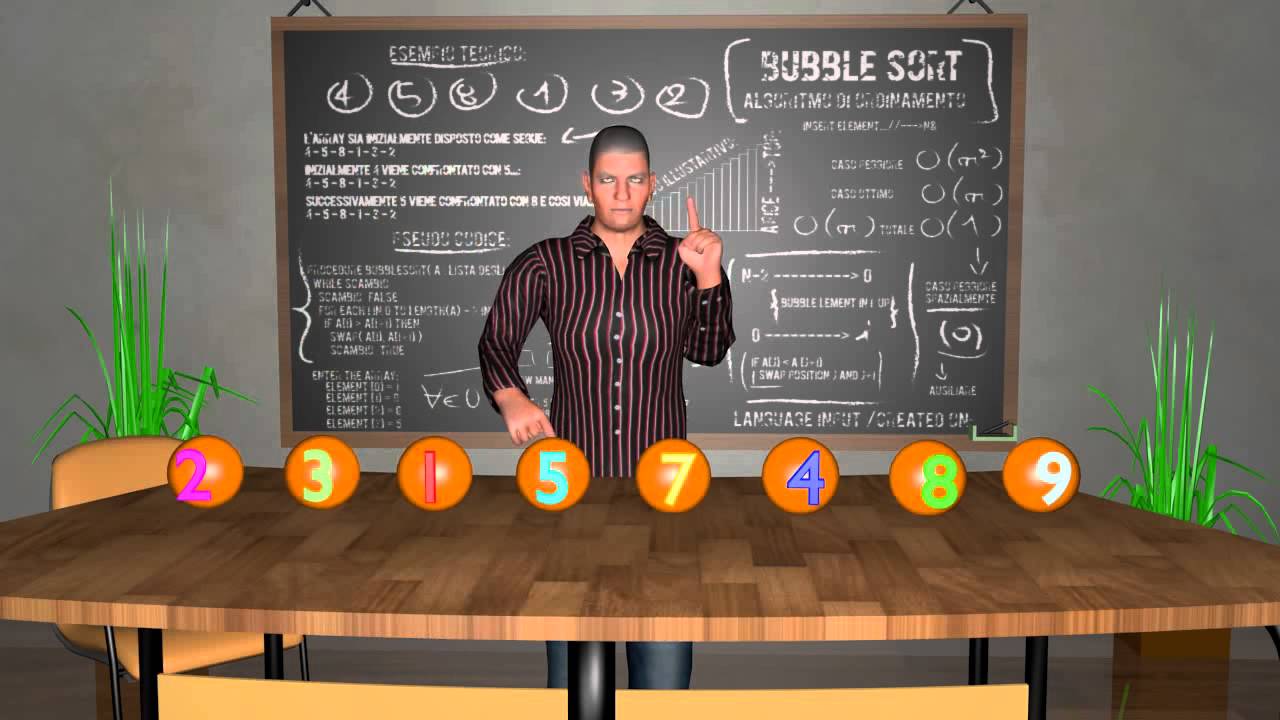
Check This New Sorting Algorithm Design
In this article, which is aimed at those who love playing around with algorithms and data structuresprogrammers, developers and codersthe author shares a new...
A Primer on Evil Twin Wireless Attacks
In a scenario where we are using freely available public wireless networks all the time, security considerations are vital. Wireless attacks can be launched...
A Detailed Review of Distributed Network Monitoring
Distributed network monitoring involves receiving performance reports about the state of the network from various locations in it, via different types of pollers. This...
Installing and Configuring Nagios Core on Linux
Heres a comprehensive guide on the Nagios network and system monitoring software application, which covers the installation and configuration of Nagios Core on a...
Relay Mails Using Gmail on RHEL6.1
This article explains the use of Postfix as a mail transfer agent to relay mails using Gmail.
In this article, lets explore how to configure...
Observium The Tireless Network Monitor
Network monitoring involves constant monitoring of how the network functions by collecting useful data from its various parts, which helps to alert the network...
Monitorix: The Lightweight System Monitoring Tool
This article introduces readers to Monitorix, which can be a boon to systems administrators as well as those who like to keep tabs on...
Things you should know about Advanced Persistent Threats
As personal, corporate and even national computer systems get subjected to stealthy, continuous cracking processes, it makes sense to be warned and armed. Read...
Licensing Your Mobile App
Speaker: Aahit Gaba, Open Source Attorney, Lyra Infosystems Pvt. Ltd
Track: Presentation
Date: 7th November 2014; Edition: OSI 2014
Introduction to Docker
Speaker: Neependra Khare, Principal Software Engineer, Red Hat
Track: Presentation
Date: 8th November 2014; Edition: OSI 2014