Tag: LFY February 2011
Securing Apache, Part 6: Attacks on Session Management
In this part of the series, we are going to concentrate on attacks on session management. Application-level attacks on the session is about obtaining...
The Needle and the Haystack: Exploring Search Models, Part 1
Searching for the proverbial needle in the haystack occurs millions of times a day in the realm of cyberspace. Ever looked under the hood...
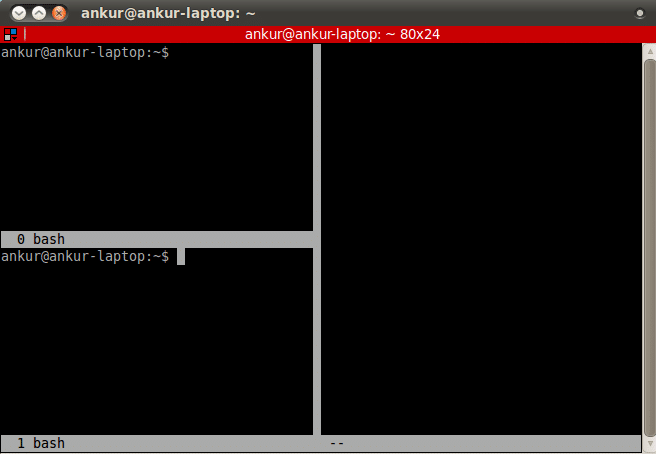
Let’s Play with GNU Screen
Many GNU/Linux users spend time working at the command line. The GNU Screen utility can be of great use if you work with multiple...
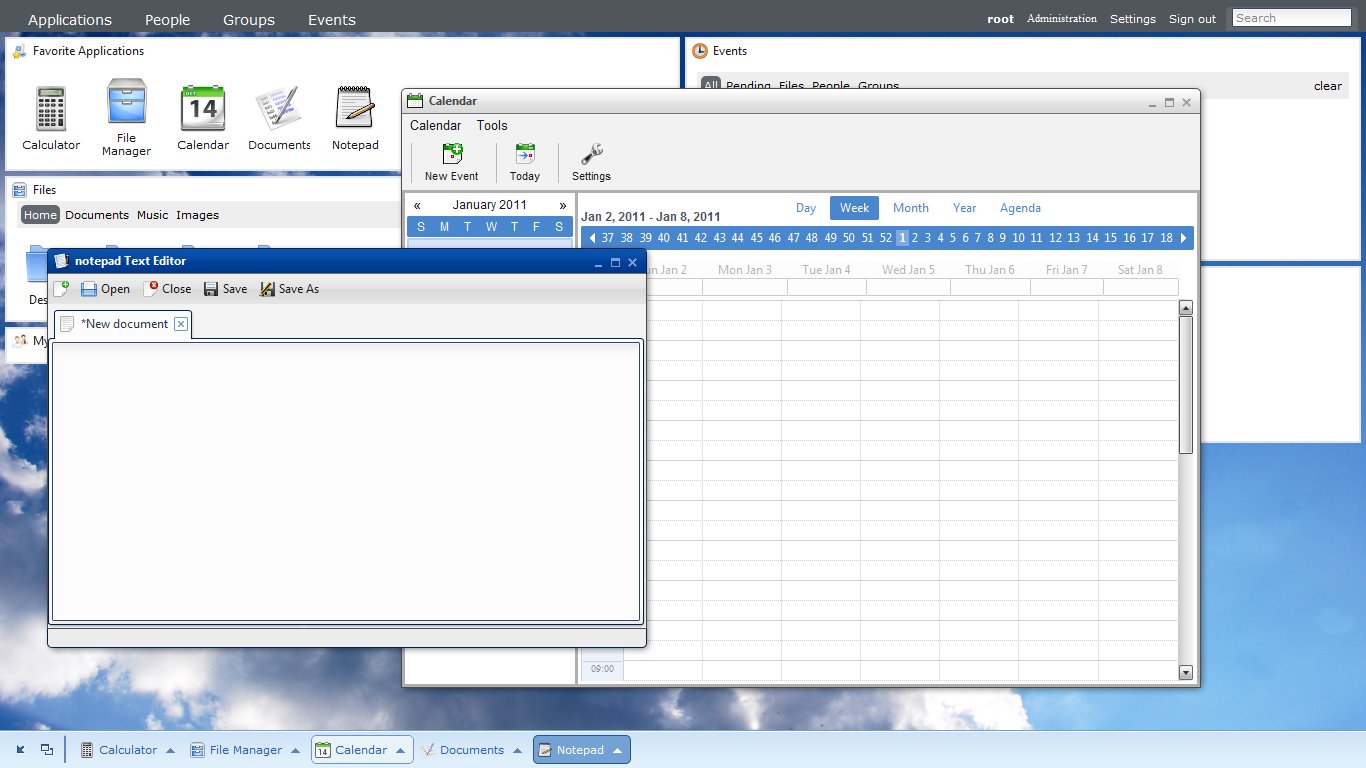
Demystifying the Cloud with eyeOS
It's another day in your life with technology and you keep hearing people talk about "Cloud this
" and "Cloud that
" or "Just store it...
Puppet Data Centre Automation Solution, Part 4: Classes & Modules
We learned about some of the interesting ways Puppet helps automate things in Part 3. In the final part of this series, we look...
Capturing Packets In Your C Program, With Libpcap
This article provides an introduction to libpcap, and shows, with examples of source code, how you can use it to create your own packet-sniffing...
Advanced Nmap: Scanning Firewalls
After four articles on Nmap , which explained a number of command-line options for scan technique specification, target specification, port specifications, host discovery, evasion...
FreedomYUG: Go Forth And Copy Left
How To Successfully Earn a Living with FOSS -- Part 1
Do you want to be an independent professional? More importantly, do you want to...
Joy of Programming: SNAFU — Situation Normal, All Fouled Up!
The stories of software development projects in crisis are amazingly familiar to all experienced programmers and managers. In this column, we'll look at some...
Exploring Software — Alternatives to Rails, Django
Zope 3 never picked up because most of the popular projects/products based on the application server never migrated from Zope 2. With "Grok --...